Architecting a Scalable Multi-Tenant Configuration Service on AWS: The Tagged Storage Pattern
In the dynamic landscape of modern microservices architectures, managing application configurations across numerous services and diverse tenants presents a formidable operational challenge. As organizations scale their cloud-native deployments, two critical gaps frequently emerge: the inherent difficulty in handling tenant-specific metadata that changes more rapidly than traditional cache invalidation strategies permit, and the subsequent struggle to scale the underlying metadata service itself without inadvertently creating a significant performance bottleneck that can cripple an entire system.
The conventional approach to caching, while essential for performance, often forces architects into an uncomfortable dilemma. They must either tolerate stale tenant context, which carries the substantial risk of incorrect data isolation leading to cross-tenant data leakage or misapplied feature flags, or implement aggressive cache invalidation. The latter, while ensuring freshness, frequently comes at the cost of sacrificing overall system performance and placing an unsustainable load on the metadata service, particularly during peak operations or widespread configuration updates. This trade-off becomes acutely problematic when tenant counts escalate into the hundreds or even thousands, transforming the metadata service from a utility into a major scaling impediment. The complexity is further compounded when different types of configurations, such as feature flags, database connection strings, or UI themes, exhibit vastly different access patterns and volatility.
The challenge intensifies when the architectural requirement mandates support for disparate storage backends, each optimally suited for specific configuration types. Some configurations, characterized by high-frequency read/write access patterns and strict low-latency requirements, are ideally served by a NoSQL database like Amazon DynamoDB. Others, perhaps less frequently accessed but demanding hierarchical organization, robust versioning, and secure storage for sensitive parameters, would benefit immensely from services like AWS Systems Manager Parameter Store. Traditional solutions often corner engineering teams: they are compelled to either build and maintain multiple, distinct configuration services, thereby dramatically increasing operational overhead and maintenance complexity, or compromise on performance and flexibility by forcing all configuration types into a single storage backend that is inherently not optimized for every use case. This compromise inevitably leads to inefficiencies, higher costs, and potential reliability issues.
This article delves into an innovative architectural approach designed to surmount these persistent challenges: the tagged storage pattern. This pattern leverages intelligent key prefixes—such as tenant_config_ for tenant-specific settings or param_config_ for global parameters—to automatically route configuration requests to the most appropriate and optimized AWS storage service. Beyond merely optimizing storage access, this pattern establishes strict tenant isolation, a non-negotiable requirement for SaaS platforms, and facilitates real-time, zero-downtime configuration updates through a sophisticated event-driven architecture, effectively eliminating the pervasive problem of cache staleness. By the conclusion of this exploration, readers will possess a comprehensive understanding of how to architect a configuration service capable of adeptly handling complex multi-tenant requirements while simultaneously optimizing for both peak performance and operational simplicity.
The Evolution of Configuration Management in Cloud-Native Architectures
The journey of configuration management has mirrored the evolution of software architecture itself. In the era of monolithic applications, configuration was often handled through local property files, environment variables, or simple databases. While straightforward for a single, self-contained application, this approach quickly became unwieldy with the advent of distributed systems and microservices. Early microservices adopters grappled with decentralized configuration, leading to inconsistency, manual errors, and deployment headaches. Centralized configuration servers, often built around solutions like Apache ZooKeeper, HashiCorp Consul, or Spring Cloud Config, emerged to bring order, but they introduced new challenges related to their own scalability, high availability, and the distribution of updates.
The shift to cloud-native platforms like AWS provided a wealth of specialized services, offering developers more granular control and powerful primitives. However, integrating these services efficiently for configuration management, especially in a multi-tenant context, required novel architectural patterns. The "tagged storage pattern" represents a maturation of this journey, moving beyond simple centralization to intelligent, context-aware storage and retrieval, tailored for the demands of hyperscale, multi-tenant SaaS applications. This evolution underscores a critical industry trend: the increasing need for architectures that are not just scalable, but also highly adaptable, secure, and cost-efficient in a rapidly changing operational environment.
Solution Overview: A Four-Layered Approach to Configuration Mastery
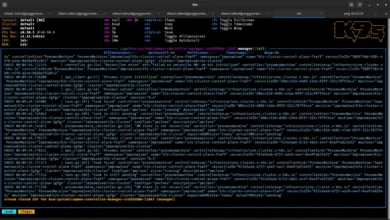
The proposed architecture orchestrates four key AWS services through a NestJS-based gRPC service, culminating in a resilient, event-driven configuration management system. Understanding the overall architecture before delving into the granular implementation details provides crucial context.
Architectural Components: A Holistic View
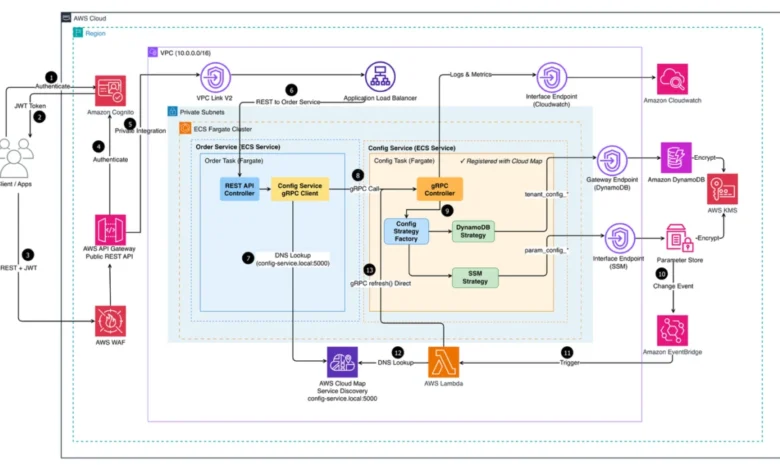
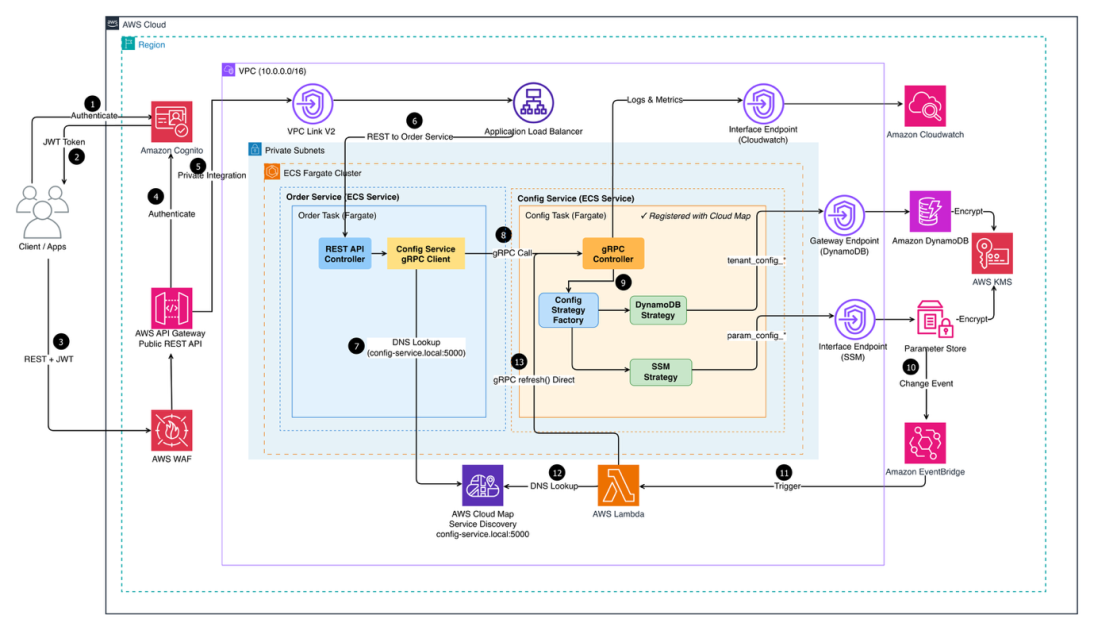
The following diagram (referencing the original image provided: https://d2908q01vomqb2.cloudfront.net/fc074d501302eb2b93e2554793fcaf50b3bf7291/2026/04/03/ARCHBLOG-1417-image-11.png) illustrates the end-to-end flow of the Multi-Tenant Configuration Service deployed on AWS. It depicts the journey from client requests entering the system to the precise retrieval of configuration data from the most appropriate storage backend.
Figure 1: Multi-Tenant Configuration Service Architecture
Client applications initiate their interaction by authenticating via Amazon Cognito, a robust and scalable identity management service. Post-authentication, traffic is first scrutinized by AWS WAF (Web Application Firewall) to mitigate common web exploits and bots, adding a critical layer of security. Subsequently, requests are routed through Amazon API Gateway, which serves as the secure, scalable front door for the API. From API Gateway, traffic traverses a VPC Link to an Application Load Balancer (ALB), ensuring private connectivity and efficient distribution of requests across the core microservices. These services operate within Amazon Elastic Container Service (Amazon ECS) on AWS Fargate, residing in private subnets for enhanced security and operational isolation.
The two primary microservices running on ECS Fargate are:
- Configuration Service: This service is responsible for retrieving configuration data. It implements the tagged storage pattern, intelligently routing requests to the correct backend.
- Management Service: This service handles the creation, updating, and deletion of configuration data, serving as the administrative interface.
Service discovery within this dynamic microservices environment is seamlessly managed by AWS Cloud Map, ensuring that services can locate and communicate with each other reliably. Meanwhile, Amazon CloudWatch plays a pivotal role in centralizing logs and metrics across all services, providing comprehensive observability crucial for monitoring health, performance, and troubleshooting.
The entire system is strategically organized into four interconnected layers, each meticulously designed to address a specific facet of the complex configuration management challenge:
1. Storage Layer: The Multi-Backend Strategy
At the foundation of this architecture lies a sophisticated storage layer that strategically employs two complementary AWS services. Each service is meticulously chosen and optimized for distinct configuration access patterns and requirements, demonstrating a principle of "right tool for the right job."
-
Amazon DynamoDB: This fully managed, serverless NoSQL database is the cornerstone for configurations demanding high-frequency access patterns and low-latency retrieval. Its exceptional scalability, consistent performance at any scale, and ability to handle millions of requests per second make it ideal for rapidly changing tenant metadata, feature flags, or application settings that are accessed frequently by numerous microservices. The composite key structure of DynamoDB, combining a partition key (PK) and a sort key (SK), is ingeniously utilized to enforce strict tenant isolation while enabling highly efficient querying. For instance, a PK could be
TENANT#<tenantId>and an SK could beCONFIG#<configKey>, ensuring that all configurations for a specific tenant are co-located and easily retrievable, without exposing other tenants’ data. -
AWS Systems Manager Parameter Store: This service provides secure, hierarchical storage for configuration data management. It excels in scenarios requiring built-in versioning, audit trails, and the secure storage of sensitive information such as database credentials, API keys, or less frequently changing application-wide parameters. Its hierarchical structure (e.g.,
/my-app/dev/db-url) simplifies organization and allows for environment-specific configurations. The Parameter Store’s integration with AWS Identity and Access Management (IAM) further enhances its security posture, making it suitable for critical system parameters that demand high integrity and traceability.
This multi-backend approach avoids the pitfalls of a monolithic storage solution, allowing the architecture to leverage the strengths of each service, leading to better performance, cost optimization, and enhanced security for different types of configuration data.
2. Service Layer: gRPC with Strategy Pattern
The core configuration retrieval logic is encapsulated within a NestJS-based microservice, employing gRPC for high-performance, type-safe communication. gRPC, a modern open-source high-performance RPC framework, offers significant advantages over traditional REST APIs for service-to-service communication. These benefits include reduced network bandwidth usage due to Protocol Buffers for serialization, improved response times, and strong type safety across different programming languages, making it an excellent choice where compatibility with web browsers is not a primary requirement.
At the heart of this service is a sophisticated Strategy Pattern implementation. This design pattern dynamically determines the optimal storage backend for a configuration request based on the configuration key prefixes. When a request for tenant_config_feature_flag_x arrives, the Strategy Pattern identifies the tenant_config_ prefix and routes the request to DynamoDB. Conversely, a request for param_config_db_connection_string would be directed to AWS Systems Manager Parameter Store. This pattern simplifies the future addition of new storage backends—such as Amazon Simple Storage Service (Amazon S3) for large configuration files or AWS Secrets Manager for very high-security secrets—without necessitating modifications to the core service logic. This promotes modularity, maintainability, and architectural flexibility, significantly reducing the overhead associated with introducing new storage mechanisms.
3. Authentication Layer: Amazon Cognito for Secure Multi-Tenancy
User authentication is a critical component, managed robustly by Amazon Cognito. Cognito handles user sign-up, sign-in, and access control, integrating seamlessly with the broader AWS ecosystem. Crucially, the system utilizes custom attributes within Cognito to store essential tenant-specific information, such as:
tenantId: A unique identifier for each tenant.tenantRole: The role or permissions associated with the authenticated user within their respective tenant.
A paramount security design principle underpins this layer: the configuration service never accepts tenantId directly from request parameters or client payloads. Instead, it meticulously extracts the tenant context solely from validated JSON Web Tokens (JWTs) issued by Amazon Cognito. This stringent policy ensures that requests cannot manipulate or impersonate other tenants, even if malicious actors attempt to alter request payloads. It provides an ironclad guarantee of data isolation, a fundamental requirement for any secure multi-tenant SaaS offering.
4. Event-Driven Refresh Layer: Real-time, Zero-Downtime Updates
Traditional approaches to configuration updates have long presented a dilemma: how to keep distributed services synchronized with the latest configurations without compromising performance or, critically, causing downtime?
- Polling approaches involve services continuously checking a central source for changes. While simple to implement, this method is inherently inefficient. It generates a constant stream of unnecessary API calls, incurring costs even when no changes have occurred, and introduces delays. Services only see updates during the next poll cycle, which could be seconds or even minutes later, leading to inconsistent application behavior.
- Service restart approaches are even more disruptive. They necessitate restarting application instances to pick up new configurations, causing immediate downtime, dropping active connections, and interrupting ongoing user sessions. For SaaS applications operating 24/7, serving a global customer base, restart-based updates are simply unacceptable.
The event-driven refresh layer is the elegant solution to both these problems, implementing a reactive architecture that ensures near real-time, zero-downtime configuration propagation. Amazon EventBridge serves as the central nervous system, monitoring changes in relevant configuration sources, primarily AWS Systems Manager Parameter Store. When a change is detected (e.g., a parameter value is updated), EventBridge triggers an AWS Lambda function. This Lambda function is responsible for signaling the configuration service instances to update their local caches. This mechanism achieves configuration updates within seconds, typically without any user-perceptible interruption or service downtime.
This reactive model provides several advantages:
- Efficiency: Updates are pushed only when necessary, eliminating wasteful polling.
- Speed: Configuration changes propagate rapidly across the distributed system.
- Reliability: Decoupled components improve system resilience.
- Cost-effectiveness: Serverless components like Lambda and EventBridge are billed per use, optimizing operational costs.
Technical Implementation: The Backbone of Tenant Isolation
The foundation of robust tenant isolation and efficient querying within this architecture is laid at the data model level, particularly with DynamoDB’s composite key structure. This design allows for both strict isolation and highly performant data access without resorting to the cumbersome and resource-intensive strategy of maintaining separate tables per tenant.
A. Multi-Tenant Data Model with DynamoDB
DynamoDB’s flexible schema and powerful indexing capabilities are leveraged to create a multi-tenant data model that is both scalable and secure. The core of this design revolves around the careful construction of the partition key (PK) and sort key (SK).
DynamoDB Schema Design Example:
To illustrate, consider a configuration item for a specific tenant.
- Partition Key (PK):
TENANT#<tenantId> - Sort Key (SK):
CONFIG#<configKey>
Let’s assume tenantId is tenant_001 and configKey is feature_flag_dark_mode.
The DynamoDB item would look like this:
| Attribute | Value |
|---|---|
PK |
TENANT#tenant_001 |
SK |
CONFIG#feature_flag_dark_mode |
configValue |
true |
description |
Enables dark mode UI for tenant |
lastUpdated |
2023-10-27T10:30:00Z |
Explanation:
- Tenant Isolation: By embedding the
tenantIddirectly into the Partition Key, all configuration items belonging totenant_001are logically grouped together. A query forPK = TENANT#tenant_001will efficiently retrieve only the configurations relevant to that specific tenant, preventing any cross-tenant data access. - Efficient Querying: The
SKallows for further refinement. If a service needs a specific configuration, it can query withPK = TENANT#<tenantId>andSK = CONFIG#<configKey>for direct, low-latency access. For retrieving all configurations of a tenant, a query on just thePKcan be performed, which is highly optimized in DynamoDB. - Flexibility: This pattern is extensible. For example, if different types of tenant configurations need to be stored (e.g.,
feature_flags,integrations,ui_settings), theSKcould be structured asCONFIG_TYPE#<configType>#CONFIG_NAME#<configName>, allowing for range queries on specific configuration types within a tenant.
This strategic use of composite keys ensures that the data model itself acts as the first line of defense for tenant isolation, making it incredibly difficult for one tenant’s data to be accidentally or maliciously accessed by another. This robust design is fundamental to the security and integrity of a multi-tenant SaaS platform.
Broader Implications and Future Outlook
The adoption of the tagged storage pattern within an event-driven, multi-backend configuration service offers profound implications for businesses operating at scale:
- Operational Simplicity and Reduced Overhead: By intelligently abstracting storage concerns and automating cache invalidation, DevOps teams are freed from complex manual configuration management tasks. This reduces the likelihood of human error, streamlines deployments, and allows engineers to focus on higher-value activities. Cloud architects frequently emphasize that "simplifying operational models is paramount for sustaining growth in cloud environments."
- Enhanced Developer Productivity: Developers no longer need to be deeply concerned with the intricacies of different storage backends or manual cache management. The configuration service provides a unified, high-performance interface, allowing them to retrieve configurations without worrying about underlying storage mechanisms, accelerating feature development and reducing time-to-market.
- Optimized Resource Utilization and Cost Efficiency: By routing configuration requests to the most appropriate storage service, the architecture ensures that resources are utilized optimally. High-volume, low-latency needs are met by DynamoDB’s cost-effective provisioned throughput, while less frequently accessed, versioned parameters leverage Parameter Store’s economical nature. This intelligent routing contributes directly to reduced infrastructure costs compared to a one-size-fits-all storage approach.
- Uncompromising Security Posture: The strict tenant isolation enforced by the data model, coupled with robust authentication via Amazon Cognito and the non-reliance on client-provided tenant identifiers, significantly elevates the security posture. This is a critical selling point for any SaaS provider, assuring customers of data privacy and integrity.
- Increased Business Agility: Real-time configuration updates, devoid of downtime, mean that businesses can respond to market changes, roll out new features, perform A/B tests, or push critical fixes almost instantaneously. This agility translates directly into a competitive advantage and improved customer experience.
- Scalability for Exponential Growth: The serverless and managed nature of the underlying AWS services (DynamoDB, Lambda, EventBridge, ECS Fargate) inherently provides immense scalability. This architecture is designed to grow seamlessly with an increasing number of tenants, configuration items, and service requests, ensuring that performance remains consistent even under extreme load. Industry reports often highlight that "architectures embracing serverless and managed services are best positioned for exponential scale without proportional increases in operational complexity."
Looking ahead, this architectural pattern provides a fertile ground for further innovation. Integration with GitOps principles could automate configuration deployment and versioning even further, treating configuration as code. Moreover, the rich telemetry collected via CloudWatch could potentially feed into AI/ML models to predict configuration needs, optimize resource allocation, or even identify anomalous configuration changes that might indicate security threats. The tagged storage pattern, therefore, is not merely a solution to present-day challenges but a foundational element for future-proof, highly resilient, and intelligently managed cloud-native applications.