Architecting a Scalable, Multi-Tenant Configuration Service with AWS and the Tagged Storage Pattern
In the dynamic landscape of modern microservices architectures, effective configuration management stands out as one of the most persistent and challenging operational concerns for organizations scaling their digital infrastructure. Two critical gaps frequently emerge as these systems expand: efficiently handling tenant metadata that demands real-time updates faster than traditional cache Time-to-Live (TTL) settings allow, and scaling the metadata service itself without inadvertently creating a significant performance bottleneck. This challenge is compounded by the need to accommodate diverse configuration types, each with unique access patterns and storage requirements. Traditional caching strategies often force an uncomfortable trade-off: either accept potentially stale tenant context, risking incorrect data isolation or misapplied feature flags, or implement aggressive cache invalidation, which can sacrifice performance and impose an unsustainable load on the underlying metadata service. As the number of tenants grows into the hundreds or thousands, the metadata service inherently transforms into a major scaling hurdle, particularly when various configuration types exhibit vastly different access patterns and data lifecycles.
The complexity further intensifies when organizations need to support multiple storage backends for different configuration types. Some configurations, such as frequently accessed tenant-specific settings, require high-frequency access patterns optimally suited for robust NoSQL databases like Amazon DynamoDB. Conversely, others, like application-wide feature flags or infrastructure parameters, benefit significantly from the hierarchical organization, built-in versioning, and secure parameter storage offered by AWS Systems Manager Parameter Store. Legacy solutions often corner engineering teams into difficult choices: either build and maintain multiple distinct configuration services, thereby increasing operational overhead and complexity, or compromise on performance and flexibility by relying on a single storage backend that is not optimally designed for every use case. This article will demonstrate how to construct a highly scalable, multi-tenant configuration service using the innovative tagged storage pattern. This architectural approach leverages key prefixes, such as tenant_config_ or param_config_, to automatically route configuration requests to the most appropriate AWS storage service. This pattern ensures stringent tenant isolation, supports real-time, zero-downtime configuration updates through an event-driven architecture, and effectively mitigates the pervasive problem of cache staleness. By the conclusion of this exploration, readers will possess a comprehensive understanding of how to architect a resilient configuration service capable of managing complex multi-tenant requirements while simultaneously optimizing for both performance and operational simplicity.
The Evolving Landscape of Microservices Configuration
The rapid adoption of microservices over the past decade has revolutionized how applications are designed, developed, and deployed. Companies like Netflix, Amazon, and Uber pioneered this architectural style, leading to a surge in its popularity across industries. A 2023 report by IBM indicated that over 70% of enterprises are either already using or planning to adopt microservices, citing benefits such as increased agility, improved fault isolation, and independent scalability. However, this architectural paradigm shift introduced new operational complexities, particularly around configuration management. In monolithic applications, configuration was typically handled via local files or a centralized database. With microservices, each service might have its own configuration, and these configurations need to be managed, updated, and distributed across a sprawling network of independent services.
Early approaches often involved polling a central configuration server, leading to latency in updates and significant network overhead. Others relied on service restarts, which are unacceptable for mission-critical applications requiring high availability. The challenge became even more pronounced with the rise of Software-as-a-Service (SaaS) models, where a single application instance serves multiple distinct tenants. Each tenant might require unique configurations, feature flags, or data isolation rules, demanding a highly granular and dynamic configuration system. The sheer volume of metadata, coupled with its dynamic nature, quickly overwhelmed traditional caching mechanisms and centralized services, necessitating a more sophisticated, distributed approach.
Introducing the Tagged Storage Pattern: A Paradigm Shift
The tagged storage pattern represents a significant architectural evolution designed to address the inherent limitations of monolithic configuration systems in a multi-tenant, microservices environment. At its core, this pattern advocates for the intelligent routing of configuration requests to specialized storage backends based on predefined "tags" embedded within the configuration keys themselves. For instance, a key prefixed with tenant_config_ might be directed to a high-throughput, low-latency key-value store like Amazon DynamoDB, ideal for frequently changing, tenant-specific settings. Conversely, a key like param_config_ could be routed to AWS Systems Manager Parameter Store, better suited for immutable, versioned, or hierarchical application-level parameters.
This pattern fundamentally decouples the configuration retrieval logic from the underlying storage mechanism. It allows architects to select the "right tool for the job" for each type of configuration data without forcing a compromise. This approach not only optimizes performance by matching data access patterns to the most efficient storage technology but also significantly enhances scalability. Instead of a single, potentially overloaded metadata service, the burden is distributed across multiple AWS services, each capable of scaling independently. Crucially, the tagged storage pattern intrinsically supports strict tenant isolation by embedding tenant identifiers directly into the configuration keys, ensuring that requests for one tenant’s data cannot inadvertently retrieve or modify another’s. Combined with an event-driven architecture, it enables real-time configuration updates without the pitfalls of cache staleness or service downtime.
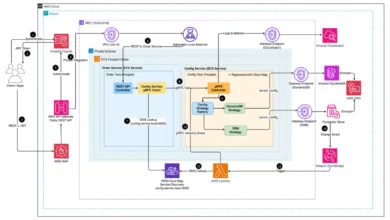
Architectural Blueprint: A Deep Dive into AWS Services
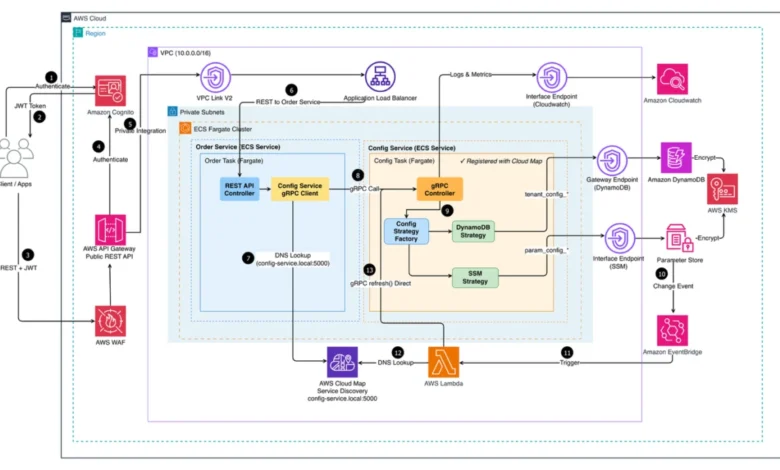
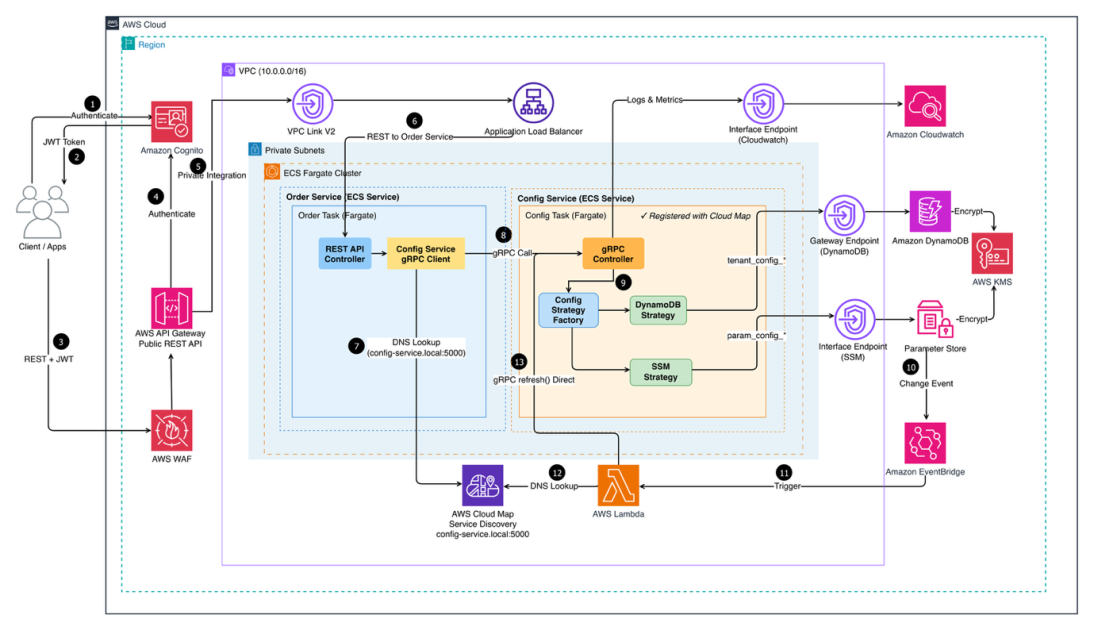
The proposed multi-tenant configuration service leverages a robust architecture comprising four interconnected layers, orchestrated primarily through a NestJS-based gRPC service. This design ensures reliability, scalability, and an event-driven approach to configuration management. The end-to-end architecture, as depicted in Figure 1 (referencing the original image: https://d2908q01vomqb2.cloudfront.net/fc074d501302eb2b93e2554793fcaf50b3bf7291/2026/04/03/ARCHBLOG-1417-image-11.png), illustrates how client requests traverse the system from authentication to configuration data retrieval.
Client applications initiate requests, authenticating via Amazon Cognito, a highly scalable user directory service, before passing through AWS WAF for enhanced security against common web exploits. Traffic is then routed through Amazon API Gateway, which provides a managed, scalable entry point for API requests. A VPC Link connects the API Gateway to an Application Load Balancer (ALB), which efficiently distributes requests across two core microservices. These services are deployed on Amazon Elastic Container Service (Amazon ECS) using AWS Fargate, providing serverless compute for containers within private subnets, ensuring security and operational simplicity. Service discovery within the containerized environment is seamlessly managed by AWS Cloud Map, while Amazon CloudWatch centralizes logs and metrics, offering comprehensive observability across all services.
The system is logically structured into four layers, each addressing a specific facet of the configuration management challenge:
The Multi-Backend Storage Layer: Optimized Data Access
The storage layer is a cornerstone of this architecture, strategically utilizing two complementary AWS services, each precisely optimized for distinct configuration access patterns and requirements.
- Amazon DynamoDB: This fully managed, serverless NoSQL database is ideal for high-frequency, low-latency access patterns. It excels at storing tenant-specific configurations that might change frequently, such as user preferences, feature flags per tenant, or dynamic application settings. Its ability to provide single-digit millisecond performance at any scale makes it suitable for critical, performance-sensitive data. Its flexible schema and robust indexing capabilities further support efficient querying based on composite keys, which is crucial for multi-tenant isolation.
- AWS Systems Manager Parameter Store: This service provides secure, hierarchical storage for configuration data management. It’s particularly well-suited for application-wide parameters, secrets, and configuration values that require versioning, auditability, and more infrequent updates. Examples include database connection strings, API keys, or global application settings. Its integration with AWS Identity and Access Management (IAM) provides granular access control, enhancing security for sensitive parameters. The hierarchical structure allows for logical grouping and easier management of related configurations.
By intelligently routing requests to either DynamoDB or Parameter Store based on the configuration key’s prefix, the system avoids the "one-size-fits-all" compromise, ensuring optimal performance and cost-efficiency for diverse data types.
The High-Performance Service Layer: gRPC and Strategy
The core configuration retrieval logic is encapsulated within a NestJS-based microservice, which utilizes gRPC for high-performance, type-safe communication. gRPC, a modern open-source high-performance RPC framework, significantly reduces network bandwidth and improves response times compared to traditional REST APIs, especially for service-to-service communication where browser compatibility is not a primary concern. Its use of Protocol Buffers for serialization ensures efficient data transfer and strong contract definitions between services, minimizing integration errors.
At the heart of this service layer is a sophisticated Strategy Pattern implementation. This design pattern dynamically determines the optimal storage backend (DynamoDB or Parameter Store) based on the configuration key prefixes. When a request for a configuration item arrives, the service inspects the key (e.g., tenant_config_123_featureA or param_config_global_settingB). Based on the prefix, it selects the appropriate "strategy" or handler, which then interacts with the corresponding AWS storage service. This pattern is crucial for architectural flexibility; it simplifies the addition of new storage backends in the future—such as Amazon Simple Storage Service (Amazon S3) for very large configuration files or other specialized data stores—without necessitating modifications to the core service logic. This plug-and-play capability drastically reduces maintenance overhead and accelerates feature development.
Robust Authentication and Tenant Isolation with Amazon Cognito
Security and strict tenant isolation are paramount in a multi-tenant environment. The authentication layer is powered by Amazon Cognito, a highly scalable, fully managed identity service. User authentication flows through Cognito, which manages user pools and identity federation. Critically, Cognito is configured with custom attributes that include essential tenant-specific metadata, such as tenantId and userRole.
A fundamental security design principle in this architecture is that the configuration service never accepts tenantId directly from client request parameters. Instead, it meticulously extracts the tenant context solely from the validated JSON Web Tokens (JWT) issued by Amazon Cognito. This crucial measure ensures that requests cannot access other tenants’ data, even if a malicious actor attempts to manipulate request payloads. By relying on cryptographically signed and validated tokens, the system guarantees that all configuration requests are inherently tied to the authenticated and authorized tenant, preventing horizontal privilege escalation and data breaches between tenants. This robust approach is a significant improvement over systems where tenantId might be passed as a query parameter or header, which can be vulnerable to tampering.
Real-time Updates: The Event-Driven Refresh Layer
One of the most vexing problems in traditional configuration management is maintaining synchronization between configuration changes and the services that consume them without compromising performance or causing downtime.
- Polling approaches continuously check for changes, generating a high volume of unnecessary API calls even when no changes have occurred. This incurs significant operational costs and introduces inherent delays, as services only see updates during the next polling cycle, which could be seconds or even minutes later. This latency is unacceptable for dynamic environments.
- Service restart approaches are even more problematic. They cause downtime, drop active connections, and disrupt user sessions, leading to a degraded user experience. For modern SaaS applications that operate 24/7, restart-based updates are simply unfeasible.
The event-driven refresh layer is engineered to tackle both these problems by implementing a reactive architecture. This layer leverages Amazon EventBridge, a serverless event bus, to monitor AWS Systems Manager Parameter Store for any configuration changes. When a parameter is modified, EventBridge detects this event and triggers an AWS Lambda function. This Lambda function is responsible for invalidating and updating the configuration service’s local cache. This mechanism ensures that configuration updates are propagated and become effective within seconds, all while users experience no interruption whatsoever. This near real-time propagation of changes significantly enhances system responsiveness, reduces operational overhead by eliminating polling, and maintains a seamless user experience, a critical factor for competitive SaaS offerings.
Data Model Foundation: Ensuring Strict Multi-Tenancy
The effectiveness of tenant isolation and efficient querying within a multi-tenant system hinges critically on a well-designed data model. In this architecture, Amazon DynamoDB’s powerful composite key structure forms the backbone, enabling both strict tenant isolation and highly efficient data retrieval without the need for separate tables per tenant, which can quickly become unmanageable.
DynamoDB Schema Design Example:
Consider a DynamoDB table named TenantConfigurations. The primary key structure would typically involve:
- Partition Key (PK):
TENANT#<tenantId> - Sort Key (SK):
CONFIG#<configKey>
Let’s illustrate with an example of a tenant-specific configuration stored in DynamoDB:
| PK | SK | configValue | lastModified |
|---|---|---|---|
TENANT#A1B2C3D4 |
CONFIG#featureFlagX |
"enabled": true, "variant": "control" |
2024-04-10T10:00:00Z |
TENANT#A1B2C3D4 |
CONFIG#appSettingY |
"theme": "dark", "locale": "en-US" |
2024-04-10T10:05:00Z |
TENANT#E5F6G7H8 |
CONFIG#featureFlagX |
"enabled": false |
2024-04-10T10:10:00Z |
TENANT#E5F6G7H8 |
CONFIG#paymentGateway |
"provider": "stripe", "keyId": "pk_test_..." |
2024-04-10T10:15:00Z |
In this schema:
- The
PKensures that all configurations belonging to a specifictenantIdare stored together in the same partition. This allows for highly efficient queries that retrieve all configurations for a given tenant with a single, performantqueryoperation. - The
SKprovides a way to uniquely identify different configuration items within that tenant’s partition. - To retrieve
featureFlagXforTENANT#A1B2C3D4, a simpleGetItemrequest withPK='TENANT#A1B2C3D4'andSK='CONFIG#featureFlagX'would suffice. - To retrieve all configurations for
TENANT#A1B2C3D4, aQueryoperation onPK='TENANT#A1B2C3D4'would be used, optionally withSKconditions for filtering.
This design inherently enforces tenant isolation. A query for TENANT#A1B2C3D4 can never inadvertently retrieve data belonging to TENANT#E5F6G7H8 because their partition keys are distinct. This model is highly scalable, as DynamoDB automatically distributes data across partitions based on the partition key, ensuring that performance remains consistent even as tenant counts and data volumes grow exponentially.
Implications and Broader Impact
The implementation of such a scalable, multi-tenant configuration service using the tagged storage pattern has profound implications for organizations operating in the cloud-native space.
- Operational Efficiency and Cost Savings: By eliminating the need for constant polling and manual service restarts, the event-driven architecture drastically reduces operational overhead. Less compute is wasted on unnecessary checks, and engineers can focus on feature development rather than firefighting configuration-related issues. The optimized use of diverse AWS storage services also ensures that organizations pay only for the most appropriate and cost-effective solution for each data type.
- Enhanced Security Posture: The rigorous enforcement of tenant isolation through JWT-validated
tenantIdand DynamoDB’s composite keys significantly strengthens the security posture. It mitigates common multi-tenancy vulnerabilities, ensuring data privacy and compliance. AWS’s native security features like WAF and Cognito further fortify the perimeter. - Improved Developer Experience: Developers are freed from the complexities of managing disparate configuration backends or wrestling with cache invalidation strategies. The clean API provided by the gRPC service and the transparent routing handled by the Strategy Pattern allow them to focus on application logic, knowing that configuration data will be delivered reliably and efficiently.
- Superior User Experience: Real-time, zero-downtime configuration updates translate directly into a seamless user experience. Feature flags can be toggled instantly, A/B tests can be rolled out with precision, and critical settings can be updated without any service interruption, which is a significant competitive advantage for SaaS providers.
- Future-Proof Scalability: The modular nature of this architecture, particularly the Strategy Pattern, makes it highly adaptable to future requirements. As new configuration types emerge or new storage technologies become available, they can be integrated with minimal disruption to the existing system. This inherent flexibility positions organizations for sustained growth and innovation.
This architecture represents AWS’s commitment to providing robust solutions that address common customer pain points in complex distributed systems. It reflects a deep understanding of the challenges faced by enterprises scaling their cloud infrastructure and provides a blueprint for building resilient, high-performance, and secure applications.
Conclusion
The journey through building and operating microservices in a multi-tenant environment is fraught with challenges, particularly in the realm of configuration management. The traditional dilemmas of cache staleness, scaling metadata services, and accommodating diverse storage needs often lead to compromises in performance, security, or operational simplicity. However, by embracing innovative architectural patterns like the tagged storage pattern and leveraging the power of AWS’s comprehensive suite of services, organizations can overcome these hurdles. The proposed architecture, utilizing Amazon DynamoDB, AWS Systems Manager Parameter Store, Amazon Cognito, and an event-driven refresh layer orchestrated via a NestJS gRPC service, delivers a robust, scalable, and secure solution. This approach ensures strict tenant isolation, enables real-time configuration updates without downtime, and optimizes resource utilization across different storage backends. Ultimately, this sophisticated yet elegantly designed system empowers enterprises to manage their multi-tenant configurations with unparalleled efficiency and confidence, paving the way for sustained innovation and superior service delivery in the cloud-native era.