Navigating the Shadow Economy Analysis of Underground Guides Reveals Professionalization of Credit Card Fraud Markets

The underground ecosystem for stolen credit card data has transitioned from a chaotic "Wild West" environment into a highly structured, process-driven marketplace where survival is predicated on vetting, operational security, and rigorous quality control. Recent intelligence gathered by cybersecurity analysts at Flare has highlighted a significant shift in how cybercriminals navigate this volatile landscape. The discovery of an internal manual titled “The Underground Guide to Legit CC Shops: Cutting Through the Bullshit” provides a rare and detailed look at the internal mechanics of modern carding operations. This document serves not only as a practical guide for fraud actors but also as a testament to the increasing professionalization of the cybercrime economy, driven by intense law enforcement pressure and a pervasive culture of internal deception.
For years, the carding industry—the trafficking and unauthorized use of stolen credit card information—was characterized by high-volume, low-security transactions. However, as international law enforcement agencies like the FBI, Europol, and Interpol have successfully dismantled major hubs such as Joker’s Stash, UniCC, and Ferum Shop, the remaining actors have been forced to adapt. The guide found on an underground forum outlines a methodology for identifying reliable suppliers, minimizing the risk of "exit scams," and maintaining anonymity in an era of advanced blockchain analysis and digital forensics.
The Shift from Opportunistic Fraud to Rigorous Supplier Vetting
One of the most significant revelations from the Flare analysis is the move away from opportunistic fraud toward a disciplined, corporate-style vetting process. In the past, threat actors might have purchased "dumps" (data from the magnetic stripe of a card) or "CVVs" (card-not-present data) from any vendor with a functional website. Today, the primary risk to a fraudster is no longer just the failure of a stolen card to authorize a transaction, but the likelihood of being defrauded by their own peers.
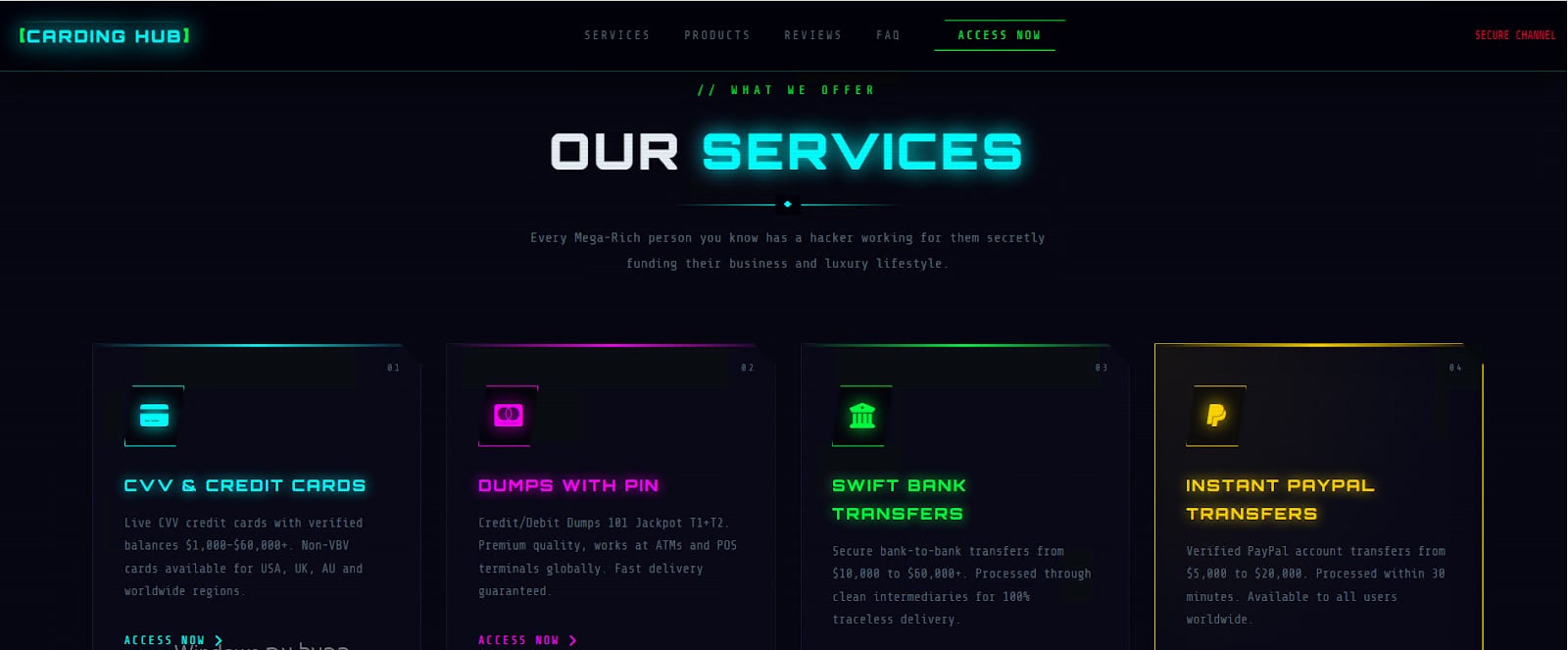
The guide emphasizes that "legitimacy" in the underground is defined by "survivability." A shop is deemed legitimate not because of its slick user interface or aggressive marketing, but because it has demonstrated the ability to remain operational despite constant threats of takedowns and infrastructure compromise. This focus on longevity suggests that the underground market is currently suffering from a crisis of trust. With the rapid turnover of marketplaces, threat actors are increasingly looking for indicators of operational maturity, such as how a shop handles its data sourcing and whether it provides consistent quality over time.
Central to this vetting process is the quality of the "fresh BINS" (Bank Identification Numbers). The BIN constitutes the first six to eight digits of a credit card and identifies the issuing bank and card type. The guide instructs actors to look for shops that source their data directly from high-yield compromises, such as infostealer infections (malware like RedLine or Lumma), phishing campaigns, or point-of-sale (PoS) breaches. Shops that consistently offer cards with low decline rates are prioritized, as this indicates the data has not been "burnt" or previously flagged by bank fraud detection systems.
A Chronology of Market Instability and Law Enforcement Pressure
To understand why such a guide is necessary, one must look at the timeline of the carding market over the last several years. The ecosystem has been plagued by a series of high-profile disruptions that have shattered the traditional sense of security among underground vendors.
In early 2021, the retirement of Joker’s Stash, once the largest carding shop in the world, created a massive power vacuum. This was followed by a wave of voluntary "retirements" and involuntary takedowns. In early 2022, Russian authorities, in a rare moment of cooperation with international interests prior to the geopolitical shifts of that year, arrested members of the Infraud Organization and shuttered UniCC. Later, in 2023, "Operation Cookie Monster" saw the seizure of Genesis Market, a major provider of stolen credentials and cookies.

These events led to a "fragmentation" of the market. Rather than a few dominant players, the ecosystem became a constellation of smaller, often short-lived shops. This environment gave rise to "exit scams," where a marketplace operator collects deposits from users and then suddenly disappears, taking the funds with them. The Flare-analyzed guide is a direct response to this instability, providing a technical checklist to help criminals avoid these traps.
Technical Standards for Fraudulent E-Commerce
The guide introduces a technical vetting protocol that mirrors the due diligence a legitimate business might perform on a new vendor. It lists several baseline requirements for a "trustworthy" carding shop:
- Domain and Infrastructure Longevity: Actors are encouraged to check the age of a shop’s domain and its WHOIS privacy settings. A shop that uses multiple mirror domains and DDoS protection is viewed as more resilient and professionally managed.
- SSL and Security Configurations: Proper implementation of SSL/TLS certificates is seen as a sign that the operators are technically proficient and care about protecting their traffic from casual interception.
- Real-Time Inventory and Support: Legitimacy is signaled by functional support systems, such as internal ticketing and the use of escrow services. These features reduce friction and build a semblance of consumer confidence within a criminal framework.
- Social Intelligence: The guide dismisses on-site testimonials as likely fake. Instead, it directs users to private, invite-only forums where long-standing reputations can be verified through historical discussion threads. This reliance on "community validation" highlights how trust is decentralized in the underground.
Operational Security and the Privacy of Financial Flows
A significant portion of the guide is dedicated to Operational Security (OPSEC), suggesting that even mid-tier fraud actors are adopting sophisticated defensive measures. These recommendations are designed to shield the actor from both law enforcement and the very shops they are using.
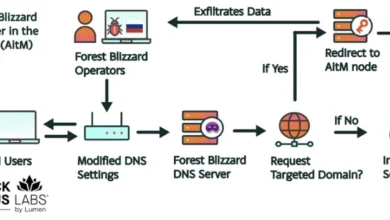
The manual strongly advocates for the use of Monero (XMR) over Bitcoin (BTC). While Bitcoin was once the standard for underground transactions, its transparent ledger has become a liability as blockchain analysis firms like Chainalysis and Elliptic have improved their ability to track "tainted" funds. Monero’s privacy-centric features make it significantly harder for investigators to link a specific transaction to a real-world identity. Furthermore, the guide warns against sending funds directly from regulated exchanges (like Coinbase or Binance), advising the use of intermediary "self-custody" wallets to break the trail.
Beyond financial privacy, the guide emphasizes the compartmentalization of the digital environment. Threat actors are told to use dedicated Virtual Machines (VMs) for their activities and to route all traffic through layers of proxies and VPNs that match the geographic location of the stolen cards they are using. This "proxy matching" is essential to bypass the automated fraud detection systems used by banks and e-commerce platforms, which often flag transactions if the IP address of the user does not align with the cardholder’s billing address.
Supporting Data: The Economic Impact of Carding
The professionalization described in the guide is a reflection of the massive sums of money at stake. According to the Nilson Report, global losses from payment card fraud are projected to reach nearly $40 billion annually by 2027. In the United States alone, the FBI’s Internet Crime Complaint Center (IC3) consistently reports billions of dollars in losses related to credit card fraud and identity theft.
The price of stolen credit card data on the dark web varies based on the "freshness" and the card’s limit. A standard card with a CVV might sell for as little as $5 to $15, while "Fullz" (records containing the cardholder’s name, address, Social Security number, and date of birth) can fetch $30 to $100. High-limit corporate or "Platinum" cards are the most sought-after, often sold at a premium because they allow for larger fraudulent purchases before triggering an alert.
The rise of "Automated Vending Cart" (AVC) shops has allowed for the scaling of these crimes. These platforms operate like a dark-web version of Amazon, allowing users to filter stolen cards by country, bank, and card type, and purchase them instantly. The guide’s categorization of these shops into "Mass Market" vs. "Boutique" indicates a maturing market that offers different service levels based on the buyer’s needs.
Official Responses and Defensive Implications
The discovery of this guide has significant implications for the cybersecurity community and financial institutions. By understanding the vetting process used by criminals, defenders can better anticipate how fraud campaigns will be structured.
Security analysts at Flare note that this intelligence allows organizations to move from a reactive to a proactive stance. For instance, if a specific carding shop is identified as having a high reputation for "fresh BINS," banks can monitor for an uptick in unauthorized transactions originating from that specific pool of card numbers. Furthermore, the emphasis on infostealers as a primary source of data underscores the need for organizations to bolster their endpoint protection and employee training to prevent the initial malware infections that fuel the carding economy.
Law enforcement agencies have also shifted their strategies. Rather than just targeting individual buyers, there is a concerted effort to strike the "infrastructure of trust." By seeding underground forums with misinformation or taking over "trusted" shops to conduct "sinkhole" operations, authorities can exacerbate the existing paranoia within the criminal community.
Broader Impact and the Future of Fraud
The "Underground Guide to Legit CC Shops" is more than just a manual; it is a symptom of a maturing criminal ecosystem that is adapting to survive in a hostile environment. The level of discipline described—ranging from technical audits of domains to the use of privacy coins and proxy chains—suggests that the barrier to entry for successful carding is rising.
However, this professionalization also creates new opportunities for disruption. As criminals consolidate around a few "vetted" and "reliable" shops, these marketplaces become high-value targets for law enforcement. The very transparency and business-like features (such as ticketing systems and escrow) that make a shop "legitimate" to a criminal also make it easier for researchers to track and analyze.
Ultimately, the carding market remains a cat-and-mouse game. As long as there is a profit motive and a supply of compromised data, these marketplaces will continue to evolve. For the global financial system, the challenge lies in maintaining a defense that is as adaptable and rigorous as the vetting processes adopted by the adversaries. The Flare report serves as a critical reminder that in the world of cybercrime, "cutting through the bullshit" is not just a catchphrase—it is a survival strategy.