Textbook Giant McGraw Hill Suffers Massive Data Breach Exposing 13.5 Million Records Following Alleged Salesforce Misconfiguration

Educational publishing behemoth McGraw Hill has found itself listed on a prominent ransomware crew’s dark web leak site, ShinyHunters, after an alleged misconfiguration within a Salesforce-hosted environment reportedly exposed the personal data of 13.5 million individuals. The incident, which came to light earlier this week, has cast a spotlight on the complexities of cloud security, third-party integrations, and the ever-present threat of data exfiltration by sophisticated cybercriminal groups. The exposed dataset, a staggering 100 GB in volume, reportedly includes sensitive personally identifiable information (PII) such as names, phone numbers, email addresses, and in some instances, physical addresses, according to information compiled by the data breach notification service Have I Been Pwned.
Discovery and Scope of the Breach
The breach became public knowledge when ShinyHunters, a notorious cybercrime syndicate known for its large-scale data theft and extortion operations, added McGraw Hill to its roster of victims on its dark web leak site. This listing, observed by cybersecurity researchers and news outlets, typically serves as a public declaration of a successful breach and an ultimatum for companies that have refused to pay a ransom demand. The group explicitly stated it possessed "over 40M Salesforce records containing PII data," indicating a broader campaign or aggregated data, and accused McGraw Hill of failing to meet an April 14 payment deadline.
While the ShinyHunters’ claim refers to "over 40M Salesforce records," the specific data linked to McGraw Hill is understood to encompass 13.5 million unique email addresses, along with other associated PII. Have I Been Pwned, a widely recognized service for checking if personal data has been compromised in a breach, has corroborated the exposure, detailing that the breach affected names, phone numbers, email addresses, and some physical addresses. The sheer volume of data, exceeding 100 GB, underscores the significant scale of the compromise, regardless of the precise number of unique individuals ultimately impacted. For a company like McGraw Hill, deeply embedded in the educational sector and entrusted with the data of students, educators, and professionals, such an exposure represents a critical security lapse.
McGraw Hill’s Official Stance and Public Silence
In response to inquiries from various cybersecurity news outlets, McGraw Hill issued statements acknowledging the activity but has conspicuously remained silent on its official corporate channels, with no mention of the incident appearing on its public website. This approach contrasts sharply with the urgency often associated with major data breaches, where rapid and transparent communication is generally advised to mitigate reputational damage and inform affected parties.
In its statements to outlets such as BleepingComputer, McGraw Hill attributed the incident to a "limited" Salesforce-hosted webpage and claimed the activity "appears to be part of a broader issue involving a misconfiguration within Salesforce’s environment that has impacted multiple organizations." The publisher was also keen to delineate the scope of the damage, asserting that the intrusion "did not involve unauthorized access to McGraw Hill’s Salesforce accounts, customer databases, courseware, or internal systems." This distinction is crucial for McGraw Hill, attempting to differentiate a third-party misconfiguration from a direct compromise of its core infrastructure. However, for the millions of individuals whose personal details are now circulating online, this technical nuance offers little comfort or assurance regarding the security of their data.
Salesforce, the cloud-based customer relationship management (CRM) giant at the center of the alleged misconfiguration, has not yet issued a public statement regarding the incident and did not respond to inquiries from The Register. This silence from both the affected company’s public channels and the platform provider leaves many questions unanswered for affected individuals and the broader cybersecurity community.
The Threat Actor: ShinyHunters’ Modus Operandi
ShinyHunters has emerged as one of the most prolific and audacious cybercrime groups in recent years, specializing in large-scale data exfiltration and subsequent extortion. The group gained notoriety for breaching numerous high-profile companies, often targeting cloud environments and third-party vendors to maximize their yield of valuable PII. Their typical modus operandi involves gaining unauthorized access to corporate networks or cloud services, exfiltrating vast quantities of data, and then demanding a ransom payment in exchange for not publishing the stolen information on their dark web leak site.
Their past victims include a diverse array of companies, and they have a documented history of targeting Salesforce-linked environments. For instance, reports indicate a 2025 campaign where ShinyHunters exploited weaknesses in connected services, rather than directly breaching Salesforce’s core systems, to access data. This pattern suggests a sophisticated understanding of cloud ecosystem vulnerabilities, particularly those arising from integrations, access permissions, and customer-side configurations. The group’s recent listing of McGraw Hill alongside other significant targets, such as Rockstar Games, underscores their continued activity and impact on global businesses. The April 14 deadline imposed on McGraw Hill is a standard tactic for ShinyHunters, designed to pressure victims into paying quickly before the data becomes publicly available and loses some of its leverage value.
Salesforce and the Shared Responsibility Model
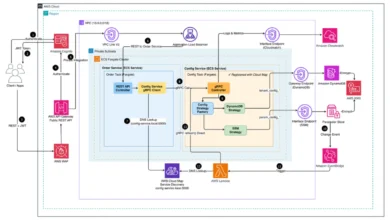
The alleged "Salesforce-linked misconfiguration" points to a common challenge in cloud computing: the shared responsibility model. In this model, cloud providers like Salesforce are responsible for the security of the cloud (e.g., the underlying infrastructure, network, and platform integrity), while their customers are responsible for security in the cloud (e.g., data, applications, configurations, access management, and integrations).
Most Salesforce compromises, as noted in the original report, do not stem from inherent flaws in Salesforce’s core platform. Instead, they typically arise from vulnerabilities on the customer’s side, such as:
- Stolen Credentials: Phishing attacks or credential stuffing leading to compromised user accounts.
- Abused OAuth Apps: Malicious or misconfigured third-party applications granted excessive permissions.
- Over-permissioned Integrations: Integrations between Salesforce and other systems that are granted broader access than necessary, creating an attack vector.
- Misconfigured Public Sites/Portals: Customer-created Salesforce sites (like Experience Cloud or other public-facing components) that are not properly secured, allowing unauthorized access to data. This "limited" webpage description from McGraw Hill suggests this might be the vector.
In the case of McGraw Hill, the emphasis on a "limited" Salesforce-hosted webpage and "misconfiguration within Salesforce’s environment" (as stated by McGraw Hill, likely referring to their own configuration within the Salesforce ecosystem) strongly suggests a customer-side error rather than a direct breach of Salesforce’s core infrastructure. While technically accurate for Salesforce, this distinction highlights the critical importance of robust security practices by cloud users. Even a seemingly "limited" exposure, if improperly configured, can become a gateway for malicious actors to harvest millions of records once it escapes into the open.
Chronology of Events
- Prior to April 2026: ShinyHunters engages in a campaign targeting Salesforce-linked environments, potentially exploiting misconfigurations or vulnerabilities in customer-managed components.
- Early April 2026: ShinyHunters successfully exfiltrates data from a McGraw Hill-managed, Salesforce-hosted environment, accumulating an estimated 13.5 million records, totaling over 100 GB.
- Early this week (leading up to April 14, 2026): ShinyHunters adds McGraw Hill to its dark web leak site, publicly claiming responsibility for the breach and accusing the company of failing to pay a ransom.
- April 14, 2026: The deadline set by ShinyHunters for McGraw Hill to pay the ransom passes, signaling the potential public release of the stolen data.
- This week: Have I Been Pwned lists the McGraw Hill breach, confirming the exposure of names, phone numbers, email addresses, and physical addresses.
- Ongoing: McGraw Hill issues statements to select media outlets, attributing the incident to a "limited" Salesforce-hosted webpage misconfiguration and denying unauthorized access to its core systems, while maintaining public silence on its own channels. Salesforce remains publicly unresponsive.
Implications for Individuals and Organizations
The exposure of 13.5 million records carries significant implications for the affected individuals and for McGraw Hill. For individuals, the immediate and long-term risks include:
- Phishing and Social Engineering: Threat actors can use the exposed names, email addresses, and phone numbers to craft highly convincing phishing emails or smishing (SMS phishing) messages, impersonating legitimate organizations to trick victims into revealing further sensitive information or downloading malware.
- Identity Theft: While more sensitive data like financial details or social security numbers were reportedly not involved in this specific breach, the combination of name, address, email, and phone number can be a crucial starting point for more sophisticated identity theft schemes.
- Spam and Unwanted Communications: Individuals may experience an increase in unsolicited emails, calls, and physical mail from scammers or aggressive marketers.
For McGraw Hill, the implications are multifaceted:
- Reputational Damage: Despite its efforts to downplay the incident, a breach of this magnitude inevitably erodes public trust, especially for an institution in the education sector.
- Financial Costs: The company faces potential costs associated with incident response, forensic investigations, legal counsel, regulatory fines (depending on jurisdictions and data types), and potential class-action lawsuits. Notifying 13.5 million individuals, even if only through email, is a substantial undertaking.
- Regulatory Scrutiny: Data protection regulations like GDPR in Europe, CCPA in California, and various state-level privacy laws may trigger investigations and impose significant penalties if non-compliance is found in the handling or protection of personal data. The presence of physical addresses and phone numbers could elevate the severity of such scrutiny.
- Operational Disruption: Diverting resources to manage the breach response can impact ongoing business operations and strategic initiatives.
The Broader Context of Digital Education and Trust
The irony of this incident for McGraw Hill, an organization fundamentally built on digital learning platforms, assessments, and educational content spanning K-12 to professional training, is hard to overlook. In an era where digital literacy and cybersecurity awareness are increasingly integrated into educational curricula, a leading educational publisher falling victim to a major data breach presents a stark lesson. It underscores that even entities at the forefront of knowledge dissemination are not immune to sophisticated cyber threats, and that the "lesson" here, particularly for those caught up in the mess, is that even "limited" exposure can escalate rapidly once it falls into the wrong hands.
The incident serves as a critical reminder for all organizations leveraging cloud services: the responsibility for data security extends beyond the cloud provider to the customer’s configuration, integration, and access management practices. In an increasingly interconnected digital landscape, every endpoint and integration point represents a potential vulnerability, and a single misconfiguration can have far-reaching consequences, affecting millions of individuals and challenging the foundational trust in digital services. The ongoing silence from McGraw Hill’s official channels and Salesforce only compounds the challenge of rebuilding that trust.