Russian Intelligence Exploits Vulnerable SOHO Routers to Harvest Microsoft Authentication Tokens in Global Spying Campaign
A sophisticated cyber-espionage operation orchestrated by military intelligence units linked to the Russian Federation has been uncovered, revealing a massive campaign to harvest authentication tokens from Microsoft Office users. Security researchers from Microsoft and Lumen’s Black Lotus Labs detailed a stealthy initiative that compromised more than 18,000 internet routers globally. Unlike traditional hacking efforts that rely on the deployment of complex malware, this campaign utilized "old-school" techniques to hijack the Domain Name System (DNS) settings of aging hardware, allowing state-backed actors to siphoning sensitive data without leaving a traditional digital footprint on the victims’ computers.
The threat actor behind the campaign is known as Forest Blizzard, a group also identified by the security community as APT28 and Fancy Bear. Attributed to the General Staff Main Intelligence Directorate (GRU) of the Russian Armed Forces, the group has a long history of high-profile interference, most notably the 2016 breaches of the Democratic National Committee and the Hillary Clinton presidential campaign. In this latest iteration of their tradecraft, Forest Blizzard shifted its focus toward the "soft underbelly" of the internet: Small Office/Home Office (SOHO) routers that are either end-of-life or severely outdated.
The Mechanics of the Attack: DNS Hijacking at Scale
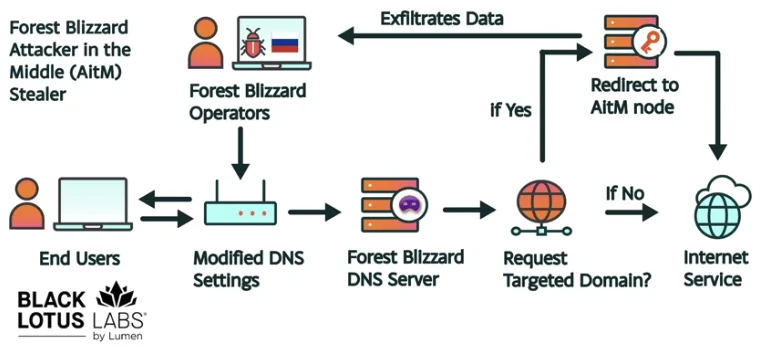
The technical core of the operation involves a technique known as DNS hijacking. In a standard internet environment, the Domain Name System acts as a directory, translating human-readable web addresses like "outlook.com" into the numerical IP addresses used by computers to locate servers. By exploiting known vulnerabilities in older routers—primarily those manufactured by Mikrotik and TP-Link—Forest Blizzard was able to gain administrative access to these devices. Once inside, they did not install malware; instead, they reconfigured the routers to use malicious DNS servers under their control.
When a user on a compromised network attempted to log in to Microsoft services, the hijacked router directed their traffic through a malicious proxy server. This setup facilitated an "Adversary-in-the-Middle" (AiTM) attack. Because the attackers controlled the routing of the traffic, they could intercept Transport Layer Security (TLS) connections. The primary goal was the theft of OAuth authentication tokens.
OAuth tokens are digital keys generated after a user successfully completes a login, including multi-factor authentication (MFA). By capturing these tokens, Forest Blizzard could gain full access to a victim’s email and cloud documents without ever needing to know the user’s password or bypass an MFA prompt in real-time. This method is particularly effective because it bypasses many modern security protocols that organizations rely on to protect against phishing.
A Shift in Tactics: From Targeted Malware to Mass Exploitation
The evolution of Forest Blizzard’s tactics suggests a highly adaptive adversary. According to Danny Adamitis, a security engineer at Black Lotus Labs, the group’s approach changed significantly following a report by the United Kingdom’s National Cyber Security Centre (NCSC) in August 2025. Prior to that report, the GRU hackers were using malware to control a small, highly targeted group of routers. However, immediately following the public disclosure of those tactics, the group abandoned their malware-centric approach.
By December 2025, the campaign had reached its peak, expanding from a few hundred targets to over 18,000 compromised routers. This shift toward mass DNS hijacking represents a "living off the land" strategy, where attackers use the legitimate functions of a system—in this case, the router’s DNS configuration—to achieve their goals. Ryan English of Black Lotus Labs described this as a "graybeard" approach, noting that while it lacks the sophistication of modern zero-day exploits, its simplicity and scale make it incredibly effective and difficult to detect.
Chronology of the Forest Blizzard Campaign
The timeline of the operation reveals a calculated response to defensive measures and a persistent effort to maintain access to Western networks:
- August 2025: The NCSC publishes an advisory detailing APT28’s use of malware on routers. In response, the group pivots within 24 hours, transitioning to a DNS-based hijacking strategy that does not require persistent malware.
- September – November 2025: Forest Blizzard begins scanning for and compromising vulnerable Mikrotik and TP-Link SOHO devices across the globe, focusing on government and law enforcement sectors.
- December 2025: The campaign reaches its zenith. Black Lotus Labs identifies more than 18,000 routers actively redirecting traffic to GRU-controlled infrastructure.
- January – March 2026: Microsoft begins identifying specific impacts on its user base, noting that over 200 organizations and 5,000 consumer devices have been directly affected by the AiTM attacks.
- March 23, 2026: The U.S. Federal Communications Commission (FCC) announces a sweeping policy change, citing the national security risks posed by foreign-made consumer routers and halting the certification of new devices produced outside the United States.
- April 7, 2026: Microsoft, Lumen, and the NCSC release coordinated reports and advisories to alert the public and provide remediation steps for the DNS hijacking campaign.
Global Reach and Impacted Entities
The scope of the spying network was vast, targeting both high-value institutional targets and individual consumers. Microsoft’s analysis identified more than 200 organizations that were compromised. The primary targets included:

- Government Agencies: Ministries of Foreign Affairs and diplomatic missions were prioritized, likely to gather intelligence on international relations and policy.
- Law Enforcement: Several law enforcement agencies were ensnared in the dragnet, providing the GRU with potential insights into ongoing investigations and internal communications.
- Third-Party Email Providers: By targeting smaller email providers, the hackers could potentially access a wider array of users who may not have the robust security infrastructure of larger tech giants.
- Consumer Devices: Approximately 5,000 consumer devices were caught in the crossfire. While these may not have been primary targets, they served as useful nodes in the broader infrastructure used to mask the attackers’ activities.
The geographical distribution of the attacks was global, though there was a notable concentration in regions of strategic interest to the Russian state. The use of SOHO routers as a launchpad allows state actors to obscure their origin, as the malicious traffic appears to originate from legitimate residential or small business IP addresses.
Regulatory Fallout and National Security Implications
The revelation of this campaign has accelerated a significant shift in U.S. telecommunications policy. The Federal Communications Commission (FCC) has moved to address the vulnerability of the nation’s digital infrastructure by targeting the hardware itself. In its March 2026 announcement, the FCC warned that foreign-made routers had become an "untenable national security threat."
The new FCC policy stipulates that the commission will no longer certify consumer-grade internet routers produced outside of the United States. This decision aims to mitigate the risk of hardware-level backdoors and the prevalence of insecure firmware in imported devices. While the policy does not mandate the removal of existing routers, it effectively bars new foreign entrants from the market unless they receive "conditional approval" from the Department of Defense or the Department of Homeland Security.
Critics of the policy have pointed out the practical challenges, noting that the vast majority of consumer networking equipment is currently manufactured in Asia. Some experts suggest that the only major consumer-grade routers currently produced in the U.S. are those associated with Starlink, which are manufactured in Texas. This has led to concerns about market competition and the availability of affordable hardware for the average consumer.
Analysis: The Resilience of "Old-School" Espionage
The Forest Blizzard campaign highlights a critical gap in global cybersecurity: the lifecycle management of internet-connected hardware. Many of the routers exploited in this campaign were "end-of-life," meaning the manufacturers no longer provide security patches for them. In other cases, users simply failed to update their firmware, leaving well-known vulnerabilities open for years.
From a strategic perspective, the GRU’s move away from malware toward DNS hijacking reflects an understanding of modern detection capabilities. Most endpoint detection and response (EDR) tools look for malicious files or unusual processes on a computer. By moving the attack to the router level, Forest Blizzard bypassed these defenses entirely. The "Adversary-in-the-Middle" attack occurs in the network layer, making it invisible to the user and most standard antivirus software.
Furthermore, the theft of OAuth tokens represents a significant escalation in the war against account takeover. As MFA becomes standard, state-sponsored actors are finding ways to steal the "proof of authentication" rather than the credentials themselves. This allows them to maintain persistent access to an account even if the user changes their password, provided the token remains valid.
Recommendations and Remediation
In light of these findings, security experts are urging both organizations and individuals to take immediate action to secure their network perimeter. The NCSC and Microsoft have provided several key recommendations:
- Hardware Audit: Organizations should identify all SOHO routers in use, including those used by remote employees. Any device that is end-of-life or no longer receiving security updates should be replaced immediately.
- Firmware Updates: Ensure all routers are running the latest available firmware. Enable automatic updates where possible.
- DNS Monitoring: Administrators should monitor for unauthorized changes to DNS settings. Using a trusted, encrypted DNS provider (such as DNS-over-HTTPS) can help prevent hijacking.
- Token Revocation: Organizations that suspect a compromise should revoke all active OAuth tokens and require users to re-authenticate.
- Zero Trust Architecture: Moving toward a Zero Trust model, where the network location (such as being on a "trusted" home router) does not grant inherent trust, can help mitigate the impact of AiTM attacks.
As the digital landscape continues to evolve, the Forest Blizzard campaign serves as a stark reminder that the most effective threats are often the ones that exploit the simplest, most overlooked components of our infrastructure. The collaboration between private sector entities like Microsoft and Lumen, alongside government agencies like the NCSC and FCC, remains the primary line of defense against state-sponsored cyber espionage.








