Russian Military Intelligence Exploits Vulnerable SOHO Routers to Harvest Microsoft Authentication Tokens Across Thousands of Global Networks
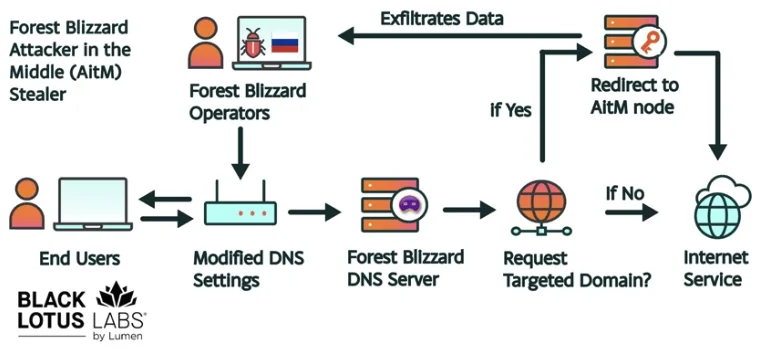
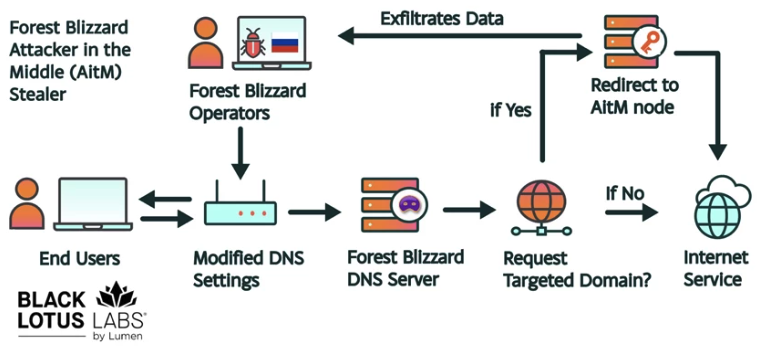
Cybersecurity researchers have uncovered a massive, state-sponsored espionage operation orchestrated by Russian military intelligence that leveraged thousands of legacy internet routers to steal sensitive authentication data from Microsoft Office users. The campaign, attributed to the notorious threat actor known as Forest Blizzard, successfully compromised more than 18,000 networks globally by exploiting known vulnerabilities in older Small Office/Home Office (SOHO) devices. Unlike traditional cyberattacks that rely on the deployment of complex malware, this operation utilized a remarkably simple yet effective technique: hijacking the Domain Name System (DNS) settings of edge devices to intercept encrypted traffic and siphon OAuth authentication tokens.
The scale of the operation became clear following a joint disclosure by Microsoft and Black Lotus Labs, the security research arm of the internet backbone provider Lumen. According to their findings, the peak of the activity occurred in December 2025, when the surveillance dragnet reached its maximum breadth. The targets were not random; the attackers specifically focused on high-value entities, including ministries of foreign affairs, law enforcement agencies, and third-party email service providers. By compromising the routers that serve as the gateway for these organizations, the Russian General Staff Main Intelligence Directorate (GRU) was able to gain a persistent foothold in sensitive communications without ever needing to touch the victims’ primary computers or servers.
The Adversary: Forest Blizzard and the Legacy of APT28
The threat actor behind this campaign, Forest Blizzard, is well-known to the international intelligence community under several aliases, including APT28, Fancy Bear, and Strontium. For over a decade, this group has functioned as a primary cyber-arm for Russia’s GRU, specializing in high-stakes political espionage and influence operations. Forest Blizzard gained global notoriety for its role in the 2016 U.S. presidential election interference, where it successfully breached the Democratic National Committee (DNC) and the Democratic Congressional Campaign Committee (DCCC).
The group’s historical tactics often involved sophisticated spear-phishing and custom-built malware. However, the recent campaign marks a strategic pivot toward infrastructure-level exploitation. By targeting the "weakest link" in the network—unpatched or end-of-life routers—the GRU has demonstrated a capacity for high-volume data harvesting that avoids detection by modern endpoint protection software. Security analysts note that while the group’s methods have evolved, their objective remains consistent: the acquisition of strategic intelligence to support Russian geopolitical interests.
Technical Mechanics: The "Graybeard" Approach to DNS Hijacking
The brilliance of the Forest Blizzard campaign lies in its simplicity, which security engineers have described as an "old-school" or "graybeard" methodology. The attackers did not rely on zero-day exploits or cutting-edge code. Instead, they targeted older Mikrotik and TP-Link routers that were either no longer supported by their manufacturers or had not been updated by their owners.
The process began with the exploitation of known security flaws in these devices to gain administrative access. Once inside the router’s configuration panel, the hackers modified the DNS settings. Under normal circumstances, DNS acts as the internet’s phonebook, translating human-readable web addresses like "outlook.office365.com" into numerical IP addresses. By pointing the routers to malicious DNS servers under their control, Forest Blizzard could redirect user traffic to "adversary-in-the-middle" (AiTM) servers.
When a user on a compromised network attempted to log in to Microsoft Outlook or other Office services, the hijacked DNS directed the connection through the attackers’ infrastructure. Because the attackers could intercept the Transport Layer Security (TLS) handshake, they were able to capture OAuth authentication tokens. These tokens are digital "keys" generated after a user successfully logs in and completes multi-factor authentication (MFA). By capturing the token rather than the password, the hackers could bypass MFA entirely, gaining direct access to the victim’s account without triggering security alerts or requiring further user interaction.
Chronology of a Shifting Strategy
The evolution of this specific campaign suggests a highly adaptive adversary that monitors the security community’s responses in real-time. According to Danny Adamitis, a security engineer at Black Lotus Labs, Forest Blizzard’s tactics underwent a significant transformation following a report released by the U.K.’s National Cyber Security Centre (NCSC) in August 2025.
Prior to that report, the GRU was using a more targeted approach, deploying specialized malware to a limited number of compromised routers. However, within twenty-four hours of the NCSC’s public disclosure of their malware, the group abandoned that technique. Instead of retreating, they scaled up. They pivoted to the mass-alteration of DNS settings, a method that is harder to attribute to a specific malware family and easier to implement across thousands of disparate devices simultaneously.
By December 2025, this systemic approach had reached its zenith. Microsoft identified more than 200 distinct organizations and 5,000 individual consumer devices that were actively being monitored. The geographic spread of the affected routers suggests a global operation, though the concentration of government-related targets indicates a clear focus on European and North American diplomatic and security sectors.
Institutional Responses and Defensive Advisories
In response to the discovery, Microsoft and the NCSC have issued urgent advisories to both enterprise administrators and home users. Microsoft’s blog post emphasized that while SOHO device compromise is a long-standing issue, the use of DNS hijacking at this scale to support AiTM attacks on TLS connections is a significant escalation. The software giant has been working to invalidate the stolen tokens and notify affected customers, though the stealthy nature of the attack makes complete remediation a challenge.
The NCSC’s advisory provided a technical breakdown of the hijacking process, urging organizations to ensure that their edge devices are not only patched but also configured to use secure, verified DNS providers. Security experts recommend that organizations implement "DNS over HTTPS" (DoH) or "DNS over TLS" (DoT) where possible, as these protocols encrypt DNS queries and make it significantly more difficult for attackers to redirect traffic at the router level.
For consumer users, the advice is more fundamental. Because many of the compromised devices were "end-of-life" (meaning the manufacturer no longer provides security updates), the only viable defense is often the physical replacement of the hardware. The prevalence of Mikrotik and TP-Link devices in this campaign highlights a broader systemic issue: the persistence of "set-it-and-forget-it" hardware in the modern threat landscape.
Regulatory Impact: The FCC’s National Security Pivot
The Forest Blizzard campaign has provided additional momentum for aggressive regulatory shifts in the United States. On March 23, the Federal Communications Commission (FCC) announced a landmark policy change that effectively halts the certification of consumer-grade internet routers produced outside of the United States. This decision followed a period of intense scrutiny regarding the security of foreign-made networking equipment, particularly from brands like TP-Link, which had already been facing potential bans.
The FCC’s updated "Covered List" now reflects a belief that foreign-made consumer routers represent an "untenable national security threat." In its statement, the commission warned that poorly secured routers are a "severe cybersecurity risk" that could be leveraged to disrupt critical infrastructure or harm U.S. citizens. While some experts have criticized the policy as being overly broad—noting that it could leave few options for consumers other than expensive domestic alternatives—the government maintains that the risk of state-sponsored exploitation outweighs the market inconvenience.
Under the new rules, router manufacturers must seek "conditional approval" from the Department of War or the Department of Homeland Security to sell their products in the U.S. market. While the policy does not mandate the immediate removal of existing routers from homes, it signals a long-term strategy to "cleanse" the domestic network of vulnerable edge devices that could serve as conduits for foreign intelligence agencies.
Analysis: The Future of Infrastructure Espionage
The success of the Forest Blizzard campaign serves as a stark reminder that the most effective cyberattacks do not always require the most sophisticated tools. By exploiting the fundamental protocols of the internet—DNS and TLS—and targeting the unmaintained outskirts of the network, the GRU has managed to bypass billions of dollars in enterprise security investments.
The implications for the future of cybersecurity are profound. As MFA becomes a standard requirement for corporate and personal accounts, state-sponsored actors will increasingly look for ways to steal the "proof of authentication" (the OAuth token) rather than the "secret" (the password). This shift requires a defensive strategy that moves beyond the endpoint and looks more closely at the integrity of the network path itself.
Furthermore, the Forest Blizzard operation highlights the growing divide between modern software security and legacy hardware vulnerability. While Microsoft can update Office 365 daily to combat new threats, they have no control over a ten-year-old router in a remote law enforcement office or a diplomat’s home. Until the lifecycle of SOHO hardware is managed with the same rigor as enterprise software, these devices will remain the preferred staging grounds for global espionage campaigns. As the GRU has demonstrated, in the world of high-stakes spying, the simplest route is often the most effective.