Massive Student Loan Data Breach Exposes Personal Information of Over 2.5 Million Borrowers Following Nelnet Servicing Vulnerability

The landscape of student loan management in the United States has been dealt a significant blow following the revelation of a massive data breach involving Nelnet Servicing, a major provider of student loan servicing systems and web portals. The breach has directly impacted over 2.5 million borrowers associated with EdFinancial and the Oklahoma Student Loan Authority (OSLA), exposing a wealth of sensitive personal information that could have long-standing repercussions for those affected. According to official disclosure filings and notification letters sent to the victims, the breach allowed unauthorized access to highly confidential data, including Social Security numbers, for nearly two months before the intrusion was fully identified and mitigated.
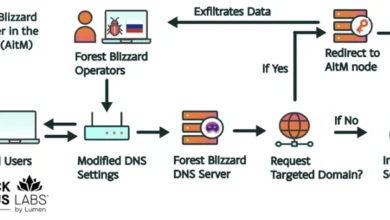
As the primary technology provider for several major loan servicers, Nelnet Servicing serves as a critical hub in the student loan ecosystem. The compromise of its systems represents a significant supply chain vulnerability, where a single point of failure at a service provider cascades into a massive privacy event for millions of individual consumers. The breach was first detected in mid-August 2022, though subsequent forensic investigations revealed that the window of vulnerability opened as early as June 1, 2022.
The Scope and Scale of the Compromise
The breach specifically targeted the servicing system and web portal managed by Nelnet Servicing, which facilitates the accounts for EdFinancial and OSLA. According to the breach disclosure filing submitted to the Maine Attorney General’s office by Nelnet’s general counsel, Bill Munn, the total number of individuals impacted stands at 2,501,324. For these individuals, the data exposed is extensive. While Nelnet has clarified that financial account numbers and payment information remained secure, the "registration information" that was accessed is more than sufficient for sophisticated identity theft operations.
The exposed data sets include full legal names, physical home addresses, email addresses, phone numbers, and Social Security numbers. In the world of cybercrime, Social Security numbers are considered the "crown jewels" of personal identifiable information (PII). Unlike a credit card number, which can be easily changed or cancelled, a Social Security number is a permanent identifier. Its exposure provides malicious actors with the foundational data needed to open fraudulent lines of credit, file false tax returns, or commit other forms of long-term identity fraud.
Chronology of the Incident
The timeline of the Nelnet breach highlights a significant gap between the initial intrusion and the eventual notification of the public. This delay is a common point of contention in cybersecurity incidents, as it often grants attackers a head start in utilizing the stolen data.
The incident began on June 1, 2022, when an unauthorized party exploited a vulnerability in Nelnet’s web portal. This vulnerability remained active and exploited for several weeks. It was not until July 21, 2022, that Nelnet Servicing identified a specific vulnerability within its system. Upon this discovery, the company’s cybersecurity team reportedly took immediate action to block the suspicious activity, patch the security hole, and secure the information system.
Despite the "immediate action" taken in July to fix the technical issue, the full scope of the data exposure was not realized until nearly a month later. On August 17, 2022, a third-party forensic investigation concluded that the unauthorized party had successfully accessed the registration information of 2.5 million borrowers throughout the June and July window. Following this determination, Nelnet began the process of notifying its partners—EdFinancial and OSLA—and preparing the mandatory disclosure letters for the affected account holders.
The Role of Nelnet in the Student Loan Infrastructure
To understand the gravity of this breach, one must understand the role Nelnet plays in the American financial system. Nelnet, based in Lincoln, Nebraska, is one of the largest student loan servicers in the country. Beyond directly servicing loans, it provides the underlying technology infrastructure for other organizations. When companies like EdFinancial or state authorities like OSLA need a robust platform for borrowers to log in, view their balances, and manage their accounts, they often outsource that technology to Nelnet.
This "servicer-of-servicers" model creates efficiency but also introduces systemic risk. If Nelnet’s portal has a vulnerability, it does not just affect Nelnet’s direct customers; it affects every organization that relies on that specific software stack. This incident serves as a stark reminder of the risks inherent in third-party vendor relationships, which have become a primary target for cybercriminals seeking to maximize the "return on investment" for a single exploit.
Official Responses and Remediation Efforts
In the wake of the discovery, Nelnet and its partners have moved into a remediation phase. The letters sent to affected borrowers emphasize that the company’s cybersecurity team worked alongside third-party forensic experts to "determine the nature and scope of the activity."
To mitigate the potential damage to borrowers, Nelnet is offering two years of free credit monitoring and identity theft protection services through Experian. This package includes a $1 million identity theft insurance policy and access to fraud resolution agents. While these measures are standard in the industry following a major breach, privacy advocates often argue that two years of monitoring is insufficient for the lifetime risk posed by a compromised Social Security number.
Official statements from Nelnet have been focused on the technical resolution. "Our cybersecurity team took immediate action to secure the information system, block the suspicious activity, fix the issue, and launched an investigation," the company stated in its disclosure. However, the specific nature of the "vulnerability" that led to the breach has not been publicly detailed, leaving security experts to speculate whether it was a zero-day exploit, a misconfigured database, or a known software flaw that had gone unpatched.
Analysis of Implications: A Perfect Storm for Scammers
The timing of this data breach is particularly concerning given the broader political and economic context of student loans in 2022. The breach was confirmed and disclosed just as the Biden-Harris administration announced its historic plan to cancel up to $10,000 in student loan debt for millions of low- and middle-income borrowers (and up to $20,000 for Pell Grant recipients).
Cybersecurity experts warn that this creates a "perfect storm" for social engineering. Melissa Bischoping, an endpoint security research specialist at Tanium, noted that the combination of the Nelnet breach and the student loan forgiveness news provides scammers with a potent toolkit. "With recent news of student loan forgiveness, it’s reasonable to expect the occasion to be used by scammers as a gateway for criminal activity," Bischoping explained.
Because the attackers now possess specific contact information (emails, phone numbers, and addresses) and know exactly who the victims’ loan servicers are, they can craft highly convincing phishing campaigns. A borrower who receives an email that appears to be from EdFinancial or OSLA, mentioning their specific account details and offering "fast-tracked loan forgiveness," is much more likely to click a malicious link or provide further sensitive information.
Furthermore, because these scammers can leverage the trust established by the existing business relationship between the borrower and the servicer, the deception is harder to spot. This type of "spear-phishing" is far more effective than broad, generic spam campaigns.
Broader Regulatory and Industry Impact
The Nelnet breach is likely to draw the attention of federal regulators, including the Department of Education and the Consumer Financial Protection Bureau (CFPB). Under the Gramm-Leach-Bliley Act (GLBA), financial institutions—including student loan servicers—are required to act with due diligence to protect the non-public personal information of their customers. Failure to maintain adequate safeguards can lead to significant fines and increased oversight.
This incident also underscores the ongoing challenges facing the education sector and its financial partners. In recent years, educational institutions and student-related services have seen a spike in cyberattacks, partly because they hold vast amounts of PII but often lack the massive cybersecurity budgets of Tier-1 global banks.
For the 2.5 million people whose data is now in the wild, the advice from experts is clear: remain hyper-vigilant. Borrowers should not only take advantage of the offered credit monitoring but should also consider placing a "security freeze" on their credit reports with the three major bureaus (Equifax, Experian, and TransUnion). A freeze prevents new credit accounts from being opened in their name and is generally considered the most effective defense against identity theft.
As the investigation into the Nelnet breach continues, the focus will likely shift to how the vulnerability existed undetected for so long and what steps the industry can take to prevent such a massive aggregation of risk in the future. For now, the millions of affected students and graduates are left to navigate the complexities of debt relief while simultaneously guarding against the renewed threat of identity fraud.