Microsoft Defender Vulnerabilities Exploited in the Wild Following Zero-Day Disclosure by Security Researcher

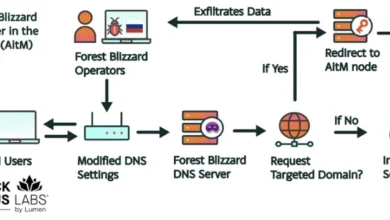
Cybersecurity firms are sounding the alarm as threat actors have begun actively exploiting a trio of recently disclosed security vulnerabilities within Microsoft Defender, the primary endpoint security solution for the Windows operating system. The vulnerabilities, which were initially released as zero-day exploits by an independent researcher, have moved from theoretical proof-of-concepts to active tools in the kits of sophisticated attackers seeking to gain elevated privileges and disable security protections on compromised systems. According to the security firm Huntress, the exploitation involves three distinct flaws codenamed BlueHammer, RedSun, and UnDefend, each of which poses a significant risk to the integrity of enterprise and individual computing environments.
The emergence of these exploits follows a contentious public disclosure by a security researcher known by the pseudonym Chaotic Eclipse (also identified as Nightmare-Eclipse). The researcher reportedly chose to release the technical details and exploit code for these vulnerabilities on GitHub as a direct response to what they characterized as an inadequate or dismissive handling of the vulnerability disclosure process by Microsoft. This "full disclosure" approach—releasing flaws before a patch is available—is a controversial practice in the cybersecurity community, often intended to pressure software vendors into faster action, but it also provides a ready-made blueprint for cybercriminals to weaponize the flaws before organizations can defend themselves.
Technical Analysis of the Exploited Vulnerabilities
The three vulnerabilities target different aspects of Microsoft Defender’s architecture, ranging from how the software handles local permissions to its mechanism for receiving vital security updates. Understanding the technical nuances of these flaws is essential for administrators attempting to secure their networks while waiting for comprehensive patches.
BlueHammer, which has since been assigned the identifier CVE-2026-33825, is a Local Privilege Escalation (LPE) vulnerability. In a typical attack scenario, an actor who has already gained a foothold on a system with low-level user permissions can use BlueHammer to elevate their status to that of a SYSTEM or administrator user. This level of access is the "holy grail" for attackers, as it allows them to bypass most security restrictions, install persistent malware, access sensitive data across the entire machine, and move laterally through the broader corporate network. Microsoft addressed this specific flaw in its most recent Patch Tuesday update, though many organizations have yet to apply the fix, leaving a window of opportunity for exploitation.
RedSun is a second LPE vulnerability that functions similarly to BlueHammer but utilizes a different attack vector within the Defender engine. Despite its similarities in impact, RedSun remains unpatched as of the latest reports. The existence of multiple LPE paths within the same security suite suggests a potentially systemic issue in how Defender manages inter-process communication or handles high-privilege operations initiated by lower-level services.
The third vulnerability, UnDefend, presents a different type of threat: a Denial-of-Service (DoS) condition. While many associate DoS attacks with crashing websites, UnDefend is specifically designed to target the defensive capabilities of the host. By exploiting this flaw, an attacker can effectively block Microsoft Defender from receiving definition updates. In the fast-moving landscape of modern malware, an antivirus solution that cannot update its "signatures" or "intelligence" quickly becomes obsolete, as it remains blind to the latest threats. Furthermore, reports suggest UnDefend may be capable of disabling certain real-time monitoring features, effectively "blinding" the security team to the attacker’s presence.
Chronology of the Exploitation and Discovery
The timeline of these events highlights the rapid transition from disclosure to weaponization in the modern threat landscape. The vulnerabilities were initially brought to light in early April 2026, when Chaotic Eclipse published the findings on GitHub. The researcher cited frustration with the Microsoft Security Response Center (MSRC), alleging that the reporting process was overly bureaucratic and that the impact of the findings was being downplayed.
On April 10, 2026, Huntress first observed the weaponization of the BlueHammer vulnerability. At this stage, the exploitation appeared to be targeted, used by actors who had already breached the initial perimeter of their victims’ networks. The activity escalated significantly following Microsoft’s Patch Tuesday on April 14, which, while fixing BlueHammer, served as a "flare" to the wider criminal community that the vulnerability was legitimate and high-value.
By April 16, 2026, the situation worsened as security researchers observed the first instances of RedSun and UnDefend proof-of-concept (PoC) code being utilized in "hands-on-keyboard" attacks. These attacks are characterized by human operators manually navigating a victim’s system rather than relying solely on automated scripts. Huntress reported that the use of these exploits was preceded by a series of standard enumeration commands, such as whoami /priv, cmdkey /list, and net group. These commands are used by attackers to survey the environment, determine their current level of access, and identify potential targets for lateral movement. The subsequent use of BlueHammer or RedSun would then be the logical next step to gain the permissions required to execute more damaging actions.
Observations from the Frontlines
Huntress, which monitors a vast array of endpoints for small and medium-sized businesses, provided critical insights into how these vulnerabilities are being used in real-world scenarios. The firm noted that the attackers are not merely "script kiddies" but appear to be organized actors who understand how to integrate these new zero-days into their existing post-exploitation workflows.
"These invocations followed after typical enumeration commands," Huntress stated in a series of technical briefings. "The sequence of events—moving from discovery to privilege escalation using these specific Defender flaws—indicates a high level of situational awareness by the threat actors. They are actively monitoring the security research community for any new tools that can help them bypass the very software designed to stop them."

In response to the detected activity, Huntress and other managed security service providers (MSSPs) have taken aggressive steps to isolate affected organizations. Isolation involves disconnecting compromised machines from the network to prevent the "phone-home" signals to attacker-controlled command-and-control (C2) servers and to stop the spread of malware to other nodes on the network.
The Ethical and Operational Debate over Full Disclosure
The exploitation of BlueHammer, RedSun, and UnDefend has reignited the long-standing debate over "responsible disclosure" versus "full disclosure." The traditional model of responsible disclosure involves a researcher privately informing a vendor of a flaw and giving them a reasonable amount of time (usually 90 days) to develop a patch before the information is made public.
However, the actions of Chaotic Eclipse represent a growing trend of "burn-it-all-down" disclosures. Proponents of this method argue that large software vendors like Microsoft often ignore vulnerabilities unless there is public pressure or an active threat. Critics, however, point to the current situation as a prime example of the harm caused by full disclosure: thousands of organizations are now at risk because the "fix" (the patch) did not arrive at the same time as the "poison" (the exploit code).
Microsoft has historically defended its disclosure timeline, citing the complexity of testing patches across millions of different hardware and software configurations to ensure that a security fix doesn’t inadvertently break the operating system. Nevertheless, the speed at which these Defender flaws were weaponized suggests that the window for "safe" disclosure is shrinking.
Industry Impact and Broader Implications
The targeting of Microsoft Defender is particularly significant due to its ubiquity. As a built-in component of Windows 10 and 11, and a core part of the Microsoft 365 Defender suite, it is one of the most widely deployed security products in the world. For many organizations, it is the only line of defense against malware and ransomware.
When a vulnerability is found in the antivirus software itself, it creates a "security paradox" where the tool meant to protect the system becomes the gateway for its destruction. This is not the first time Defender has been targeted; historically, attackers have sought "living-off-the-land" techniques where they use trusted Windows binaries to carry out malicious tasks. Using Defender to escalate privileges is an evolution of this strategy.
The broader implications for the cybersecurity industry are twofold. First, there is an urgent need for organizations to move toward a "defense-in-depth" strategy. Relying on a single security product, no matter how robust, creates a single point of failure. Organizations that utilized secondary monitoring tools or EDR (Endpoint Detection and Response) solutions alongside Defender were more likely to catch the enumeration commands that preceded the exploitation of BlueHammer and RedSun.
Second, the event highlights the critical importance of patch management agility. While Microsoft released a fix for BlueHammer within days of the first exploitation, the lag time in corporate deployment remains a major hurdle. Attackers thrive in the "patch gap"—the time between the release of a security update and its actual installation on a target system.
Official Responses and Mitigation Strategies
While Microsoft has not yet provided a detailed public statement regarding the UnDefend and RedSun flaws, the company’s action in patching CVE-2026-33825 indicates they are treating the matter with high priority. In previous similar instances, Microsoft has recommended that users ensure "Cloud-delivered protection" and "Automatic sample submission" are turned on, as these features can sometimes provide heuristic detections for exploit behavior even if a specific patch for the vulnerability is not yet available.
For organizations currently at risk, security experts recommend several immediate steps:
- Apply CVE-2026-33825 Immediately: Systems should be updated to the latest version of the Microsoft Malware Protection Engine.
- Monitor for Enumeration Activity: Security teams should look for unusual use of commands like
net group,whoami /priv, andcmdkey. While these are legitimate Windows tools, their use in rapid succession is often a sign of a manual intruder. - Restrict Local Administrative Rights: Since BlueHammer and RedSun are LPE flaws, they require an initial foothold. Implementing the Principle of Least Privilege (PoLP) can prevent an attacker from gaining the initial access needed to trigger the exploit.
- Network Segmentation: Ensure that if one workstation is compromised via a Defender exploit, the attacker cannot easily jump to high-value targets like domain controllers or database servers.
The situation remains fluid as researchers continue to track the activities of groups exploiting these zero-days. As of this writing, the cybersecurity community is waiting for further updates from Microsoft regarding the remaining two vulnerabilities. The incident serves as a stark reminder that in the realm of digital defense, the tools designed to keep us safe are themselves part of the attack surface, requiring constant vigilance and a proactive approach to security management.