Fraud Operations and the Evolution of Trust in the Underground Credit Card Economy

The underground market for stolen credit card data, colloquially known as the carding economy, is currently undergoing a significant structural transformation driven by a combination of internal volatility and external pressure from global law enforcement. Historically characterized by opportunistic theft and chaotic distribution networks, the ecosystem is shifting toward a more disciplined, process-oriented model. This evolution is detailed in a comprehensive analysis by security firm Flare, which recently uncovered an internal instructional document titled “The Underground Guide to Legit CC Shops: Cutting Through the Bullshit.” This guide serves as a manual for cybercriminals, teaching them how to navigate an environment increasingly plagued by "exit scams," law enforcement "honeypots," and low-quality data.
The emergence of such a guide highlights a critical paradox in the cybercriminal world: as the volume of stolen data increases, the ability to find reliable, high-quality sources becomes more difficult. For financial institutions and cybersecurity professionals, this shift represents a move toward professionalization among threat actors, where the focus has moved from the act of theft to the rigorous vetting of the supply chain.
The Historical Context of Carding and Market Volatility
To understand the current state of the carding market, one must look at the timeline of its development. In the early 2000s, platforms like ShadowCrew pioneered the organized sale of stolen financial data. However, the subsequent decades saw a cycle of boom and bust. Major law enforcement interventions, such as the 2022 takedown of Hydra Market and the 2023 seizure of Genesis Market (Operation Cookie Monster), created a vacuum that led to the proliferation of smaller, less reliable shops.
In this fractured landscape, distrust became the primary barrier to entry. Criminal actors frequently fall victim to "rippers"—scammers who set up fake marketplaces to steal the deposits of other criminals. According to industry data, nearly 30% of new underground marketplaces are suspected to be exit scams or law enforcement fronts within their first six months of operation. The guide discovered by Flare is a direct response to this instability, providing a methodology for threat actors to identify "survivability" as the ultimate metric of a shop’s legitimacy.
A Methodology for Vetting Illicit Suppliers
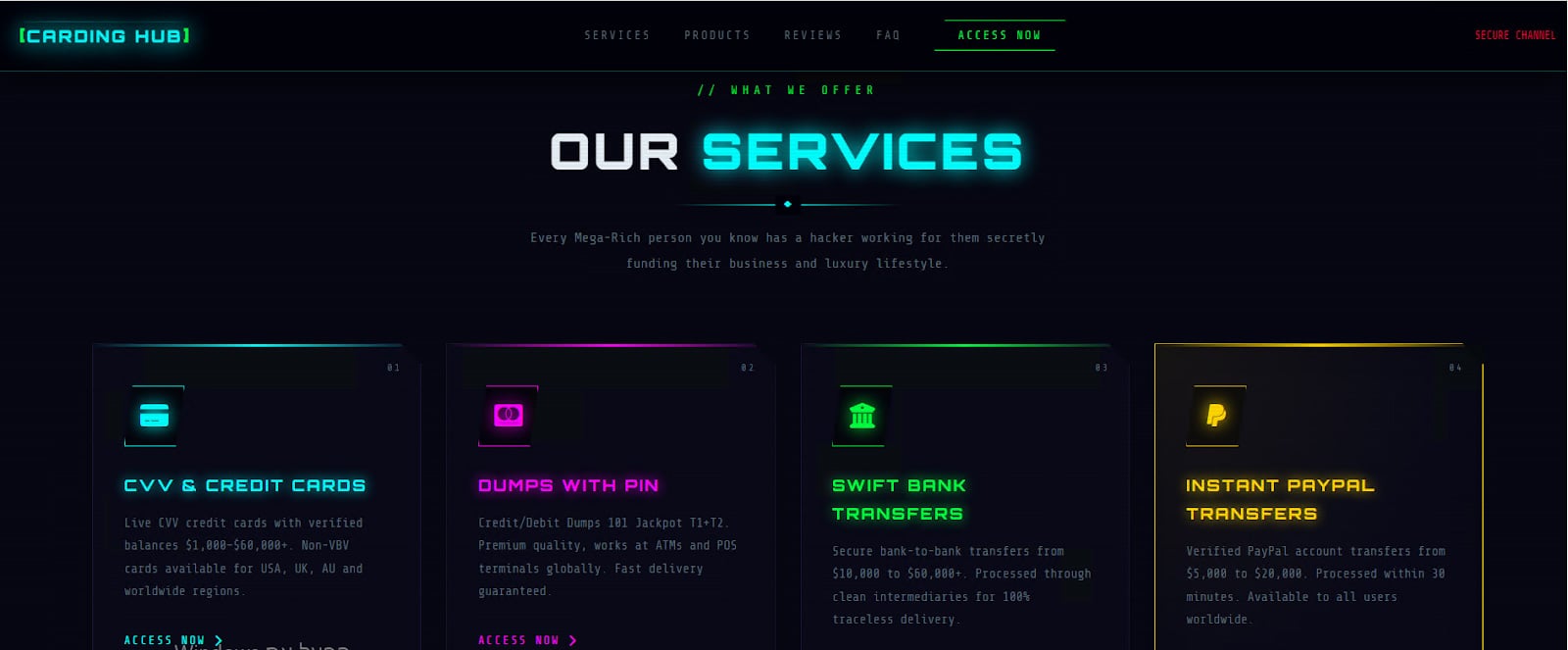
The Flare report reveals that modern carding actors are no longer swayed by flashy web design or aggressive marketing. Instead, they utilize a technical checklist to verify the infrastructure of a marketplace before committing funds. This vetting process closely mirrors legitimate corporate due diligence, focusing on the longevity and technical robustness of the platform.
Key technical indicators used by threat actors include:
- Domain Longevity and WHOIS Analysis: Actors are instructed to check the age of a domain. A shop that has existed for several years is seen as more reliable than one registered recently.
- SSL Configuration and Security Layers: The presence of high-grade encryption and DDoS protection (such as mirrors or specialized hosting) suggests that the operators have the capital and technical expertise to defend their platform against both rival gangs and law enforcement.
- Infrastructure Redundancy: The guide emphasizes the importance of "mirror domains." Legitimate shops in the underground space rarely rely on a single URL, instead maintaining multiple access points to ensure operational continuity in the event of a domain seizure.
This shift toward technical verification suggests that the barrier to entry for successful fraud is rising. Low-level "script kiddies" are being filtered out by the complexity of these requirements, leaving behind a more sophisticated class of cybercriminals who operate with the mindset of a procurement officer.

Data Quality: The Role of BINs and Infostealers
In the carding ecosystem, the value of a stolen record is determined by its Bank Identification Number (BIN) and its "freshness." The guide emphasizes that a shop’s reputation is built on its ability to provide cards with low decline rates. This focus on data quality points to a sophisticated backend supply chain.
Most high-quality data is sourced through three primary channels:
- Infostealer Malware: Tools like RedLine or Lumma Stealer infect consumer devices, harvesting credit card details directly from browser autofill data.
- Phishing and Smishing: Large-scale campaigns that trick users into entering their financial information into fraudulent portals.
- Point-of-Sale (PoS) Breaches: Malware installed on the payment systems of retail or hospitality businesses, allowing for the bulk harvesting of physical card data.
The guide encourages buyers to look for "Fresh BINs"—data that has been recently harvested and has not yet been flagged by bank fraud detection systems. For banks, this means that the window of opportunity to detect and neutralize a compromise is shrinking. As criminals become better at vetting their sources, the speed at which stolen data is monetized increases.
Operational Security and the Shift to Privacy-Focused Finance
A significant portion of the newly discovered guide is dedicated to Operational Security (OPSEC). This is perhaps the most telling sign of the pressure law enforcement is exerting on the underground. Threat actors are being advised to abandon traditional methods of evasion in favor of layered, multi-step security protocols.
One of the most prominent recommendations involves the use of cryptocurrency. While Bitcoin was once the standard for underground transactions, its transparent blockchain has made it a liability. The guide strongly advocates for the use of Monero (XMR), a privacy-focused coin that obscures sender and receiver addresses. Furthermore, actors are told to avoid direct transfers from regulated exchanges like Coinbase or Binance, which have stringent Know Your Customer (KYC) requirements. Instead, they use "intermediate wallets" and "mixers" to break the trail of digital breadcrumbs.
Beyond finance, the guide suggests using virtual machines (VMs) and dedicated proxy services that match the geographical location of the stolen card data. This "geo-matching" is a tactic designed to bypass the fraud filters used by e-commerce platforms, which often flag transactions if the IP address of the buyer does not match the billing address of the card.
Market Segmentation: Scale vs. Exclusivity
The Flare analysis notes a clear division in the market structure of carding shops. There are two primary models currently in operation:
1. Automated Platforms: These function like illicit versions of Amazon. They offer searchable databases where buyers can filter by country, bank, card type, and even the zip code of the victim. These platforms prioritize volume and efficiency, catering to mid-tier actors who conduct hundreds of small-scale fraudulent transactions.
2. Boutique Vendor Groups: These are often invite-only and operate on platforms like Telegram or closed forums. They prioritize exclusivity and high-success rates over volume. These groups often build long-term relationships with "wholesalers" and provide bespoke data for high-value fraud, such as corporate card compromise or large-scale wire transfers.
This segmentation allows the underground economy to remain resilient. If a large automated platform is taken down by the FBI or Europol, the boutique groups continue to operate quietly, ensuring that the supply of stolen data is never fully extinguished.
Implications for the Global Financial Sector
The professionalization of the carding market has dire implications for global finance. According to the Nilson Report, global losses from payment card fraud are projected to exceed $165 billion over the next decade. As threat actors adopt the "vetting discipline" described in the Flare report, the efficiency of their attacks will only improve.
Industry analysts suggest that the response from the financial sector must be equally disciplined. Traditional reactive measures—such as canceling a card after a fraudulent charge—are no longer sufficient. Banks are increasingly turning to behavioral biometrics and AI-driven pattern recognition to identify fraud in real-time. However, as criminals use the guide’s advice to "geo-match" IPs and use clean proxies, the "digital footprint" of a fraudster becomes nearly indistinguishable from that of a legitimate customer.
The discovery of this guide also serves as a reminder of the "human element" in cybercrime. Trust is the rarest commodity in the underground. By understanding how criminals build and verify trust among themselves, law enforcement and security teams can identify new "choke points" for disruption. For instance, injecting "poisoned data" or low-quality records into these markets can erode the reputation of a shop, causing the internal distrust that leads to market collapse.
Conclusion: A More Resilient Threat Landscape
The underground guide titled “The Underground Guide to Legit CC Shops” is more than just a manual for fraud; it is a testament to the adaptability of the cybercriminal ecosystem. Faced with aggressive law enforcement and internal treachery, the carding community has not retreated. Instead, it has matured, adopting the structures of legitimate business to ensure its own survival.
For defenders, the takeaway is clear: the adversary is becoming more selective, more technical, and more cautious. The era of the "unorganized" carder is ending, replaced by a new generation of actors who view fraud as a disciplined profession. To counter this, the security industry must move beyond simple perimeter defense and begin to engage with the intelligence found in these underground forums, using the criminals’ own vetting processes against them to disrupt the flow of stolen data at its source.








