Huntress Alerts Organizations to Active Exploitation of Three Microsoft Defender Vulnerabilities Amid Zero-Day Disclosure Crisis

Cybersecurity firm Huntress has issued an urgent advisory regarding the active exploitation of three recently revealed security vulnerabilities within Microsoft Defender, the primary endpoint security solution for hundreds of millions of Windows users worldwide. The vulnerabilities, which were released as zero-days by a security researcher in an act of protest against Microsoft’s internal disclosure and patching protocols, are currently being leveraged by threat actors to gain elevated privileges and disable critical security defenses on compromised systems.
The exploitation involves a trio of flaws colloquially named BlueHammer, RedSun, and UnDefend. These vulnerabilities were publicly disclosed by a researcher known as Chaotic Eclipse (also identified as Nightmare-Eclipse) via GitHub. According to reports, the decision to bypass the traditional coordinated vulnerability disclosure (CVD) process was a direct response to what the researcher characterized as Microsoft’s mishandling of the reporting timeline and a perceived lack of urgency in addressing the underlying architectural weaknesses in the Defender platform.
The Anatomy of the Vulnerabilities
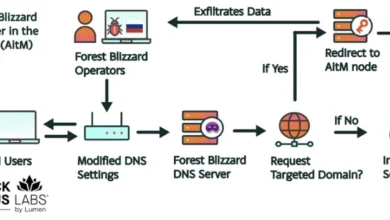
The three flaws represent distinct but complementary threats to Windows environments. Two of the vulnerabilities, BlueHammer and RedSun, are categorized as Local Privilege Escalation (LPE) flaws. LPE vulnerabilities are particularly dangerous in the hands of an attacker who has already gained an initial foothold in a network, such as through a phishing campaign or the exploitation of a web-facing application. By utilizing an LPE exploit, a low-privileged user or a malicious script can "escalate" its permissions to that of a SYSTEM or Administrator account. This level of access grants the attacker total control over the endpoint, allowing them to install persistent backdoors, exfiltrate sensitive data, or move laterally across the internal network.
The third vulnerability, UnDefend, poses a different but equally severe risk. It is classified as a Denial-of-Service (DoS) flaw specifically targeting the update mechanism of Microsoft Defender. When successfully exploited, UnDefend can effectively block the security software from receiving critical definition updates. In the fast-moving landscape of modern cybercrime, an antivirus solution that cannot update its signature database or behavioral detection logic becomes rapidly obsolete, leaving the host system vulnerable to new strains of malware and ransomware that would otherwise be blocked.
A Timeline of Escalation and Exploitation
The timeline of events highlights a rapid transition from public disclosure to active weaponization. Huntress began observing malicious activity related to these flaws as early as April 10, 2026, when BlueHammer was first observed in the wild. This initial wave of exploitation occurred just days after the researcher’s public repository went live.
On April 14, 2026, Microsoft moved to mitigate the immediate risk by addressing BlueHammer as part of its monthly Patch Tuesday cycle. The vulnerability has since been assigned the identifier CVE-2026-33825. Despite the release of this patch, the threat remains significant for organizations that have yet to apply the update or those utilizing older versions of the Windows operating system that may not receive immediate support.
The situation worsened on April 16, 2026, when Huntress analysts detected the first instances of RedSun and UnDefend proof-of-concept (PoC) exploits being used in active attacks. Unlike BlueHammer, these two vulnerabilities currently lack an official patch from Microsoft, meaning that even fully updated systems—excluding the specific fix for CVE-2026-33825—remain susceptible to these exploits.
Huntress noted that the exploitation of these flaws typically occurs during the "hands-on-keyboard" phase of an attack. Analysts observed threat actors running a series of enumeration commands immediately following the deployment of the exploits. These commands include:
whoami /priv: Used to check the current user’s privileges and confirm if escalation was successful.cmdkey /list: Used to view stored usernames and credentials on the system.net group: Used to identify administrative groups and domain architecture.
The presence of these commands suggests that the attackers are not merely automated bots but human operators manually navigating the compromised environment to maximize the impact of their intrusion.
The Researcher’s "Zero-Day" Protest
The public release of BlueHammer, RedSun, and UnDefend has reignited the long-standing debate within the cybersecurity community regarding "full disclosure" versus "coordinated disclosure." The researcher, Chaotic Eclipse, indicated that the decision to release the code publicly was a "last resort" following a breakdown in communication with the Microsoft Security Response Center (MSRC).

In statements shared on social media and GitHub, the researcher alleged that Microsoft failed to acknowledge the severity of the reports and provided a timeline for remediation that was deemed unacceptable given the potential risk to the public. By releasing the vulnerabilities as zero-days, the researcher sought to force Microsoft’s hand and provide the community with the information necessary to build their own detections while a patch was pending.
However, the consequences of this action are now being felt by security teams worldwide. While full disclosure can provide transparency, it also provides a ready-made roadmap for malicious actors. In this instance, the interval between the publication of the PoC and the first observed attack was less than a week, leaving many enterprise IT departments struggling to keep pace.
Implications for Enterprise Security
The exploitation of Microsoft Defender is particularly concerning due to its role as a "trusted" component of the Windows ecosystem. Because Defender operates with high-level system permissions to scan files and monitor process behavior, any vulnerability within the tool itself provides a direct path to the heart of the operating system.
Security experts refer to this as the "security-of-security" problem. When the tools designed to protect a system are themselves the point of failure, traditional defense-in-depth strategies are compromised. If an attacker can use UnDefend to stop updates, they can effectively "blind" the security team, making subsequent malicious actions—such as the deployment of a ransomware payload—much harder to detect.
Furthermore, the exploitation of LPE flaws like RedSun allows attackers to bypass Windows’ built-in security boundaries, such as User Account Control (UAC). This bypass is often the final step needed for an attacker to disable other third-party security agents, clear event logs to hide their tracks, and begin the process of data exfiltration.
Microsoft’s Response and Industry Reaction
Microsoft has acknowledged the reports and is reportedly working on security updates for the remaining two vulnerabilities. In a preliminary statement, a Microsoft spokesperson emphasized the company’s commitment to security and urged customers to maintain "up-to-date systems and follow best practices for identity management."
The broader cybersecurity industry has reacted with a mix of technical vigilance and calls for better researcher-vendor relations. Managed Detection and Response (MDR) providers, including Huntress, have been working to deploy custom detection rules to identify the specific "signatures" of the BlueHammer and RedSun exploits.
"We have taken immediate steps to isolate affected organizations where we have seen this activity," Huntress stated in a series of updates. "The use of these exploits in conjunction with manual enumeration indicates that threat actors are moving quickly to capitalize on the public availability of this research."
Recommendations for Mitigation
In the absence of a complete set of patches for RedSun and UnDefend, security professionals recommend several immediate steps to reduce the risk of exploitation:
- Prioritize CVE-2026-33825: Organizations should immediately apply the April 2026 security updates to address the BlueHammer vulnerability.
- Monitor for Enumeration Activity: Security Operations Centers (SOCs) should increase monitoring for common post-exploitation commands (e.g.,
whoami /priv,net group,quser). Unusual activity from low-privileged accounts should be treated as a high-priority incident. - Endpoint Isolation: If signs of exploitation are detected, the affected host should be isolated from the network immediately to prevent lateral movement.
- Audit Defender Update Status: Use centralized management tools (such as Microsoft Intune or SCCM) to monitor the "last updated" status of Defender signatures. Any systems that consistently fail to update should be investigated for potential UnDefend exploitation.
- Implement Least Privilege: Ensure that users are not running with administrative rights for daily tasks, as this limits the initial damage an attacker can do before they are forced to attempt a privilege escalation.
Looking Ahead
The ongoing exploitation of Microsoft Defender highlights the volatile nature of the modern threat landscape. As researchers and vendors continue to clash over disclosure timelines, the end-user organization remains caught in the middle. The "BlueHammer" incident serves as a stark reminder that even the most ubiquitous and trusted security tools require constant vigilance and a robust, rapid patching strategy.
As Microsoft prepares further updates, the cybersecurity community remains on high alert. The transition from a researcher’s protest to an active threat actor’s toolkit demonstrates that in the digital age, a zero-day disclosure is a double-edged sword that can cut through the very defenses it was intended to improve. Further updates from Microsoft regarding the status of RedSun and UnDefend are expected in the coming days.