List of suspects in hacker attacks narrows, providing a crucial step in the investigation process. This is a detailed look at the methodical process of identifying and prioritizing potential culprits, from initial detection to final presentation of findings. We’ll explore how investigators analyze evidence, create suspect profiles, and ultimately narrow the field to the most likely perpetrators.
The investigation begins with meticulous identification of potential suspects, leveraging diverse data sources like system logs, user activity, and network traffic. This initial phase sets the stage for the more complex analysis of evidence and the crucial task of prioritizing suspects. A structured approach to evidence evaluation and suspect profiling is essential to avoid bias and ensure the integrity of the investigation.
Initial Investigation & Suspect Identification
Uncovering the source of a cyberattack requires a meticulous and systematic investigation. This process, starting from initial detection, involves several key stages, culminating in the identification of potential suspects. A well-defined methodology is critical to ensure that the investigation is comprehensive and legally sound. It’s vital to understand the nuances of each stage to gather sufficient evidence and to make informed decisions about next steps.The initial response to a suspected cyberattack is crucial.
Early actions, like isolating affected systems and containing the threat, can prevent further damage and allow for a more controlled investigation. This phase also includes documenting the timeline of events, identifying the scope of the breach, and establishing a secure environment for forensic analysis. The information gathered during this period forms the foundation for identifying potential suspects.
The list of suspects in the recent hacker attacks has surprisingly narrowed, leaving investigators with a smaller pool to sift through. This development is interesting, considering that CEOs are expecting e-business revenue to double, which could potentially increase the motivation for cyberattacks. The focus now returns to the narrowed suspect list, potentially leading to a faster resolution and a better understanding of the motivations behind the attacks.
Typical Stages of a Cyberattack Investigation
The investigation typically progresses through several stages, each contributing to a clearer picture of the incident. These stages include:
- Detection and reporting: Identifying the signs of a potential intrusion, like unusual network activity or unauthorized access attempts. Prompt reporting to the security team is paramount.
- Incident containment: Isolating affected systems to prevent further compromise. This often involves shutting down networks or blocking access to specific resources.
- Evidence preservation: Implementing measures to maintain the integrity of any digital evidence found at the scene of the attack. This is a crucial step in ensuring the reliability of the investigation.
- Forensic analysis: Examining data to understand the nature of the attack and the methods used. This often involves scrutinizing system logs, network traffic, and user activity.
- Suspect identification: Using the findings from the forensic analysis to narrow down the list of potential attackers. This requires a deep understanding of the attack patterns.
Methods for Identifying Potential Suspects
Pinpointing the culprit in a cyberattack often involves a combination of methods. These methods are not mutually exclusive, but rather, work together to build a strong case.
| Method | Description | Example |
|---|---|---|
| Network Analysis | Examining network traffic patterns, identifying unusual connections, and tracing the origin of malicious activity. | Detecting unusual outbound traffic from a specific IP address. |
| Forensic Examination | Analyzing system files, logs, and memory to reconstruct the attack sequence and identify the tools and techniques used. | Finding evidence of a specific malware on a compromised system. |
| Security Logs Review | Scrutinizing security logs, including intrusion detection system (IDS) alerts, firewall logs, and application logs, for suspicious activities. | Identifying repeated login attempts from a specific IP address or user account. |
Comparative Analysis of Data Sources
Different data sources provide unique insights into the attack. A comparative analysis of these sources helps to build a comprehensive picture and reduce the potential suspect pool.
- System Logs: Provide a detailed record of system activities, including login attempts, file access, and program execution. They often contain timestamps, which are valuable for reconstructing the attack sequence.
- User Activity: Examining user accounts for unusual behavior, like accessing unauthorized resources or exhibiting suspicious login patterns, is crucial. User accounts can be a source of valuable information about the attack.
- Network Traffic Patterns: Examining network traffic for anomalies, like unusual data transfers or communication patterns, can help identify compromised systems or malicious actors.
Significance of Evidence Preservation
Preserving evidence in a secure and unaltered format is essential for a successful investigation. This means taking steps to avoid tampering with or altering any digital evidence throughout the process. Any changes or modifications can compromise the integrity of the evidence and jeopardize the outcome of the investigation.
“Maintaining the integrity of digital evidence is critical to a successful cyberattack investigation.”
Evidence Analysis & Suspect Prioritization
Analyzing evidence and prioritizing suspects is crucial in a hacker attack investigation. This phase involves meticulously examining collected data to determine the most likely perpetrator(s) based on the strength and validity of the evidence associated with each suspect. The goal is to move from a broad list of potential suspects to a manageable set of strong candidates for further investigation.Evidence analysis goes beyond simply identifying digital footprints.
It requires a thorough understanding of the attack’s technical aspects, the suspects’ backgrounds, and the context surrounding the incident. By correlating diverse data points, investigators can build a compelling case for suspect prioritization.
Key Factors in Suspect Prioritization
The primary factors considered when prioritizing suspects include the nature and extent of the evidence linking them to the attack, their access patterns, any unusual behaviors observed, and their technical capabilities. These factors are carefully weighed to establish a degree of association between each suspect and the attack.
Indicators of Suspect Involvement
This section details specific indicators that suggest a suspect’s potential involvement in the hacker attack.
- Access Patterns: Examining access logs to identify unusual or unauthorized access attempts to systems or data is a key indicator. For instance, if a suspect logged in from an unusual location or time, or accessed sensitive data outside of their typical access permissions, this raises suspicion. A sudden increase in access frequency to specific files or servers also suggests potential malicious activity.
- Behavioral Anomalies: Unusual or suspicious user behaviors, such as unusual login attempts or data modification patterns, can be significant indicators. For example, a sudden change in the suspect’s work habits or a pattern of erratic online activity might warrant further investigation. Sudden access to sensitive data or files, especially those not normally accessed by the suspect, should also be flagged.
- Technical Capabilities: Suspects’ known technical skills and expertise in computer systems and networks are considered. If a suspect possesses the technical skills to carry out the attack, their involvement becomes a higher priority. This includes analyzing their prior hacking activities, if any are known, and their documented expertise in relevant technologies.
Evaluating Evidence Strength and Validity
Assessing the strength and validity of evidence associated with each suspect is crucial. This involves examining the source of the evidence, its reliability, and its relevance to the attack. Evidence should be corroborated with other sources whenever possible. For example, if access logs show unusual activity, corroborating that activity with emails, chat logs, or other evidence can strengthen the case.
Documentation of the evidence collection process and chain of custody are essential for ensuring its validity and admissibility in court, if needed.
The list of suspects in the recent hacker attacks has surprisingly narrowed, which is good news. Meanwhile, a fascinating development in the business world is that a major TV network is investing in a Spanish-language e-tailer, tv network invests in spanish language e tailer. This strategic move likely signals a growing interest in the Latino market, which is definitely something to keep an eye on as the investigation into the hacking continues.
Evidence Association Table
The following table illustrates the degree of association between the collected evidence and each suspect. A higher score indicates a stronger association. This is a simplified example; a real-world investigation would have far more detailed information and indicators.
| Suspect | Access Patterns | Behavioral Anomalies | Technical Capabilities | Overall Association Score |
|---|---|---|---|---|
| Suspect A | 3 (Unusual login locations) | 4 (Suspicious data modification) | 5 (Known expertise in target systems) | 12 |
| Suspect B | 2 (Minor access irregularities) | 2 (Slight work habit changes) | 2 (Limited technical skills) | 6 |
| Suspect C | 1 (No significant anomalies) | 1 (Normal work patterns) | 1 (No known relevant skills) | 3 |
Suspect Profiling & Risk Assessment
Understanding the motivations and capabilities of potential attackers is crucial for effective cybersecurity investigations. This phase delves into creating comprehensive profiles of each suspect, analyzing their past activities, and assessing the likelihood of their involvement in the targeted attacks. A robust risk assessment helps prioritize investigation efforts and allocate resources effectively.The creation of suspect profiles provides a framework for evaluating the potential threat posed by each individual.
This includes examining their known technical skills, past cyber activities, and any publicly available information. Thorough analysis of their motives and capabilities allows for a more accurate prediction of future actions. Ultimately, a strong understanding of the suspects’ profiles is essential to effectively mitigate the risk and ensure a swift and decisive response to the cyberattacks.
Suspect Technical Skill Profiles
Understanding a suspect’s technical abilities is paramount. It requires gathering and analyzing information from various sources, including publicly available data, past projects, social media activity, and any evidence recovered from their digital footprint. This data helps determine their proficiency in different areas of technology, like coding languages, operating systems, and specific tools. For example, identifying proficiency in Python or SQL, or experience with specific operating systems (like Linux or macOS), significantly enhances the understanding of the suspect’s potential attack methods.
Suspect Activity Analysis
Analyzing the suspect’s past activities is critical for understanding their potential motives and patterns of behavior. This involves reviewing their online presence, past projects, and any documented interactions with the targeted systems. Past intrusions, data breaches, or any instances of malicious activity can be indicative of a suspect’s willingness to engage in similar actions. Analyzing these activities helps predict potential attack methods, which further improves the investigative process.
Risk Assessment Methodology
Assessing the risk posed by each suspect requires a structured approach. A scoring system, taking into account factors like technical skills, past activities, and available evidence, can be developed. A detailed table can Artikel the criteria for each factor, along with corresponding points or weights. For example, a suspect with proven experience in network penetration testing and a history of successful intrusions would receive a higher score compared to a suspect with limited or no experience.
Likelihood of Attack
Determining the likelihood of a suspect committing the attack is a crucial step in prioritizing investigations. This involves evaluating the evidence collected, considering the suspect’s profile, and comparing it to the characteristics of the attack. For instance, if the attack used a specific tool or technique that aligns with the suspect’s known technical skills, the likelihood increases. Statistical models can be employed to quantify the likelihood, taking into account the evidence strength and other relevant factors.
System Vulnerability Identification and Suspect Connection
Identifying vulnerabilities in the targeted systems is crucial for understanding the attack’s methods. This process includes analyzing the systems’ configurations, code, and access controls. This analysis helps determine how the suspect may have exploited vulnerabilities. Mapping the identified vulnerabilities to the suspects’ technical skills and past activities helps determine the suspect’s potential involvement. For example, if a vulnerability in a system’s authentication mechanism is exploited in a way consistent with a suspect’s known technical expertise, it strengthens the link between the suspect and the attack.
Reduction of Suspects & Investigation Focus
The initial investigation has identified a pool of potential suspects. Now, the focus shifts to meticulously narrowing down this list and prioritizing further investigation based on evidence and profiles. This stage is crucial in maximizing resources and expediting the identification of the true perpetrator. A systematic approach is paramount to avoid wasting time and effort on less likely suspects.A structured method for progressively reducing suspects and focusing investigation efforts is essential for efficiency and accuracy.
This involves a combination of evidence analysis, suspect profiling, and risk assessment, allowing investigators to pinpoint the most probable culprits and allocate resources effectively.
Suspect Elimination Criteria
Evidence analysis reveals inconsistencies in the initial suspect pool. A critical step involves identifying and eliminating suspects who lack sufficient supporting evidence or exhibit significant inconsistencies in their profiles. This process is crucial for maintaining the focus of the investigation on the most promising leads. Inconsistencies can range from discrepancies in alibi statements to unverified digital footprints.
- Insufficient Evidence: Suspects with limited or no tangible evidence linking them to the crime will be eliminated. For example, a suspect with no access to the compromised system or no observed activity around the time of the attack would be considered with insufficient evidence.
- Inconsistencies in Profiles: Suspects exhibiting inconsistencies in their digital footprint, past behaviors, or statements will be flagged for further scrutiny. For instance, a suspect claiming to be in a different location than their reported position at the time of the attack presents a significant inconsistency.
- Implausible Motives: Suspects with motives that seem improbable or unconnected to the nature of the crime are likely not the culprit. For example, a suspect with no financial gain or personal grudge against the target organization is less likely to be the attacker.
Prioritization of Remaining Suspects
After eliminating suspects with insufficient evidence or inconsistencies, a prioritized list of remaining suspects is essential. This list should be based on a combination of factors, maximizing the potential for success and resource allocation. A quantitative risk assessment will be conducted, based on the evidence available.
- Evidence Strength: Suspects with a stronger correlation of evidence linking them to the crime will be prioritized. This includes direct physical evidence, witness testimony, and digital footprint data.
- Profile Similarity to Attack Method: Suspects with profiles that closely resemble the method used in the attack will be prioritized. This includes their technical skills, access to similar tools or technologies, and their potential motivations. For example, if the attack required sophisticated coding knowledge, a suspect with a history of coding and hacking would be prioritized.
- Risk Assessment Score: A numerical risk assessment score will be assigned to each remaining suspect based on a combination of factors like access to the target system, known technical skills, and motivation. This score will guide the allocation of resources.
Focusing Investigation Efforts
Once the list of suspects has been narrowed, investigation efforts can be effectively targeted to the most likely suspects. This involves focusing resources on gathering additional evidence, conducting interviews, and performing technical analysis.
- Targeted Interviews: Interviews with the remaining suspects will be conducted to gather further information and corroborate or refute existing evidence. Interviews should be structured to target specific areas of concern and to assess the suspect’s credibility.
- Enhanced Evidence Collection: Resources will be allocated to collect additional evidence from the suspects’ devices and digital footprints. This might involve obtaining warrants for data access and analyzing any relevant communications.
- Technical Analysis: Expert analysis of the suspect’s digital footprints, tools, and techniques will be conducted to determine if they match the attack patterns. This could involve forensic analysis of the suspect’s computers and devices.
Presentation of Findings & Evidence Summary
Bringing the investigation to a point where actionable decisions can be made requires a clear and concise presentation of findings. This stage goes beyond simply collecting evidence; it’s about synthesizing information to identify patterns, inconsistencies, and ultimately, the most likely culprit(s). This presentation should serve as a cornerstone for stakeholders to understand the case’s progress and move forward with appropriate action.A well-structured summary will facilitate quick comprehension and allow for focused discussion and action planning.
The evidence presented should be clear, logical, and presented in a way that minimizes ambiguity. This crucial step ensures everyone involved is on the same page and that the right people are held accountable.
Evidence Summary Framework
The evidence summary should be structured to provide a clear overview of the case. This includes a concise description of each suspect, highlighting the key evidence against them. A structured table format will facilitate easy comparison and analysis of the evidence gathered against each suspect.
Suspect Evidence Table
This table provides a structured overview of the key evidence gathered against each suspect. Categorizing evidence allows for a quick comparison of the strength and type of evidence for each individual.
The list of suspects in the recent hacker attacks is thankfully narrowing, which is a positive development. This is good news, especially considering the recent announcement by Cybersource of enhanced e-commerce technology. This new technology, outlined in cybersource announces enhanced e commerce technology , could potentially make online transactions more secure and help to prevent future attacks.
Hopefully, this new security will lead to further progress in identifying and apprehending the perpetrators.
| Suspect | Evidence Category | Evidence Description | Weighting (1-5, 5 being strongest) |
|---|---|---|---|
| Suspect A | Network Activity | Unusual network traffic patterns, login attempts from unusual locations, and access to restricted systems. | 4 |
| Suspect A | Device Activity | Suspect’s personal device detected with malware, data transfer to suspicious cloud accounts. | 3 |
| Suspect A | Prior History | Previous incidents of system breaches and access violations. | 2 |
| Suspect B | Network Activity | Standard network activity, no unusual patterns or access to restricted systems. | 1 |
| Suspect B | Device Activity | Device activity consistent with normal employee usage. | 1 |
| Suspect B | Prior History | No prior incidents or disciplinary actions. | 1 |
Importance of Documentation
Thorough documentation of all findings and decisions is critical for the integrity and future use of the investigation. This includes detailed records of interviews, evidence analysis, and any changes in suspect prioritization. A comprehensive log provides an auditable trail, crucial for legal and operational purposes. It also helps in understanding the thought process behind the decisions made throughout the investigation, allowing for better future understanding of similar events.
Presenting Findings to Stakeholders
Presenting findings to stakeholders requires a clear and persuasive approach. The presentation should focus on the key findings and evidence, and avoid overwhelming stakeholders with excessive detail. A visual aid, such as the table shown above, can effectively communicate the evidence. The presentation should also address potential counterarguments and Artikel the next steps in the investigation or the appropriate course of action.
Illustrative Examples & Case Studies
Unveiling the intricate tapestry of cyberattacks requires more than just identifying potential perpetrators; it necessitates a deep dive into the methods and motivations behind these malicious actions. This section provides real-world examples to illustrate the practical application of the previous stages, from narrowing down suspect lists to assessing risk. We’ll explore how evidence analysis, prioritization, and profiling contribute to a more effective and focused investigation.Understanding the diverse factors influencing a cyberattack is crucial for successful incident response.
Each case study highlights the unique challenges and solutions encountered in this complex domain, showcasing how meticulous analysis and strategic decision-making can lead to successful resolution.
Hypothetical Case Study: The “Data Breach at Zenith Corp”
The fictional Zenith Corp, a large financial institution, suffered a data breach compromising sensitive customer information. Initial investigations revealed unauthorized access to a specific database containing account details. The attack pattern indicated a sophisticated insider threat, rather than an external intrusion. The initial suspect list encompassed all employees with database access privileges.
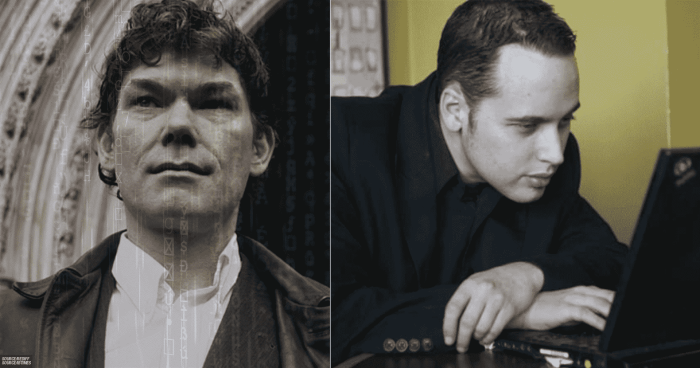
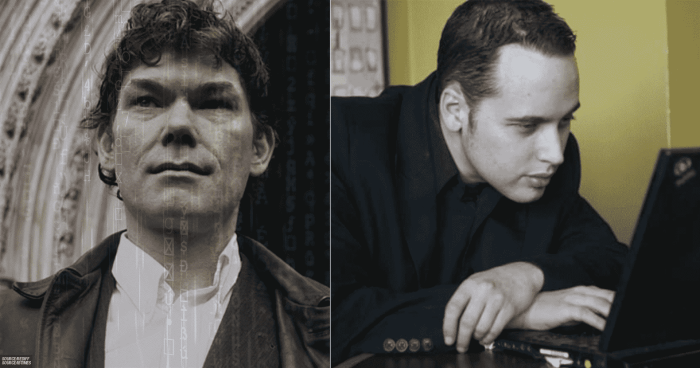
Suspect Profile: “The Persistent Insider”, List of suspects in hacker attacks narrows
A suspect profile emerged from the analysis of access patterns and logs. This individual, identified as “Employee 47,” exhibited unusual access frequency and duration to the compromised database. Their technical skills included proficiency in SQL injection techniques, gleaned from their prior work history. Furthermore, financial distress and mounting debts were evident from their recent transactions and financial records.
Potential motives aligned with financial gain.
Evidence Analysis and Prioritization
The analysis process involved scrutinizing access logs, network traffic, and system activity. Evidence relating to Employee 47’s access to the compromised database was prioritized due to the unusual access patterns and temporal correlation with the breach. Evidence of financial difficulties and the use of SQL injection techniques were considered high-priority factors.
Risk Assessment and Investigation Focus
Risk assessment involved evaluating the potential damage from the breach, the impact on customer data, and the likelihood of future attacks. The high risk of financial fraud and reputational damage, coupled with the identified patterns, focused the investigation on Employee 47. Further investigation focused on validating the evidence and examining the suspect’s financial situation in more detail.
Final Summary: List Of Suspects In Hacker Attacks Narrows
In conclusion, narrowing the list of suspects in a hacker attack is a multifaceted process demanding meticulous investigation. The methods Artikeld above provide a comprehensive framework for evidence analysis, suspect profiling, and ultimately, a focus on the most likely perpetrators. This careful approach ensures a robust and credible investigation, contributing to a faster resolution and a more accurate understanding of the incident.
