
Latest hacker attacks rattle e commerce – Latest hacker attacks rattle e-commerce, leaving a trail of financial devastation and reputational damage. From the substantial financial losses incurred by targeted companies to the erosion of customer trust, the consequences are far-reaching. This deep dive explores the multifaceted impact of these attacks, examining the various tactics employed, the vulnerabilities exploited, and the evolving security measures being implemented.
We also investigate customer responses, future trends, and the regulatory landscape surrounding these escalating cyber threats.
The escalating sophistication of cyberattacks targeting e-commerce platforms is alarming. Companies are facing increasingly complex challenges in protecting their systems and customer data. This article delves into the specifics, providing a comprehensive overview of the evolving threats and potential solutions.
Impact on E-commerce Businesses
Recent hacking incidents targeting e-commerce platforms have highlighted the critical need for robust security measures. These attacks are not just isolated incidents; they represent a significant threat to the financial stability and reputation of online retailers. The financial repercussions, reputational damage, and erosion of customer trust can be substantial and long-lasting.
Financial Ramifications of Hacking Incidents
E-commerce companies face substantial financial losses from hacking incidents. Direct costs include paying for forensic investigations, data recovery, and system restoration. Indirect costs, often more significant, encompass lost revenue from downtime, compromised customer data leading to chargebacks and refunds, and potential legal and regulatory penalties. The cost of a security breach can range from hundreds of thousands to millions of dollars, depending on the scale of the attack and the company’s size.
For example, a large online retailer experiencing a significant data breach could lose millions in lost sales, customer refunds, and legal fees.
Reputational Damage from Security Breaches
Security breaches severely damage the reputation of e-commerce companies. Customers lose trust in the platform’s ability to protect their personal information and financial data. Negative publicity and media coverage can tarnish the brand image, leading to a decline in customer loyalty and future sales. This damage is often long-lasting and can take years to repair. A well-known case illustrates how a breach can result in a loss of public trust, leading to a decline in customer base and a significant drop in sales.
Impact on Customer Trust
Customer trust is a crucial asset for e-commerce businesses. Security breaches erode this trust, impacting future sales and brand loyalty. Customers may become hesitant to shop online, potentially switching to competitors perceived as more secure. Surveys and customer feedback following breaches often reveal a significant decrease in trust and a willingness to shop elsewhere. For example, a significant data breach at a popular online retailer might cause a large portion of customers to lose faith in the company and seek alternative shopping options.
Strategies for Mitigating Financial Losses
E-commerce platforms employ various strategies to minimize financial losses from security breaches. Proactive measures include implementing robust security protocols, such as multi-factor authentication, firewalls, and intrusion detection systems. Regular security audits and penetration testing can identify vulnerabilities and address them before they are exploited. Incident response plans are also essential for quickly containing breaches and minimizing damage.
Companies may also invest in insurance policies to cover potential losses. These comprehensive approaches, encompassing preventative and reactive measures, are crucial for safeguarding against future breaches.
Comparative Costs of Security Measures
The table below provides a comparative analysis of the costs associated with various security measures, categorizing them as preventative or reactive.
The recent spate of hacker attacks targeting e-commerce sites is seriously concerning. Consumers are understandably worried about their online security, and the need for robust payment systems is paramount. A new online payment service, like the one aiming to streamline bill paying processes, online payment service aims to streamline bill paying process , could potentially offer a more secure and efficient way to handle transactions.
However, even with these advancements, the issue of hacker attacks still looms large in the e-commerce world.
| Security Measure | Category | Estimated Cost (USD) | Justification |
|---|---|---|---|
| Multi-factor authentication | Preventative | $5,000 – $50,000 | Reduces unauthorized access. |
| Firewall and intrusion detection system | Preventative | $10,000 – $100,000 | Prevents unauthorized access and malicious activity. |
| Regular security audits | Preventative | $5,000 – $50,000 | Identifies vulnerabilities and potential threats. |
| Penetration testing | Preventative | $10,000 – $100,000 | Simulates attacks to test security measures. |
| Incident response plan | Reactive | $5,000 – $50,000 | Handles breaches quickly and effectively. |
| Data breach insurance | Reactive | $10,000 – $100,000+ | Covers financial losses associated with breaches. |
Note: Costs are estimates and can vary greatly depending on the size and complexity of the e-commerce platform. Preventative measures, though initially higher in cost, can significantly reduce the likelihood and impact of future breaches, thereby mitigating long-term financial losses.
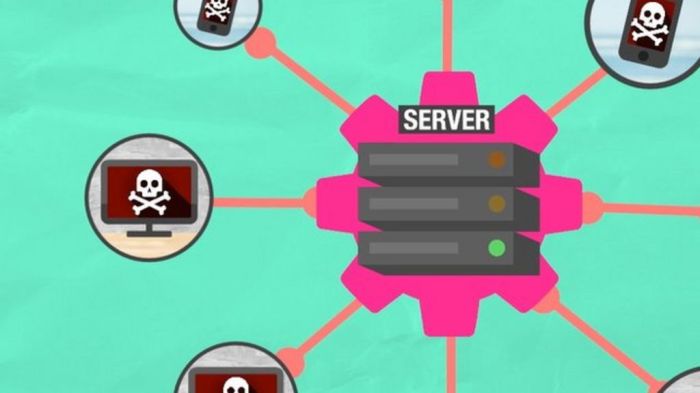
Types of Attacks and Tactics
E-commerce platforms are attractive targets for cybercriminals due to the vast amount of sensitive data they handle. Understanding the tactics employed in these attacks is crucial for businesses to implement robust security measures and mitigate risks. This section will delve into the prevalent hacking methods targeting e-commerce, detailing the methods used to steal customer data or disrupt services.
Prevalent Hacking Methods
E-commerce platforms are vulnerable to a variety of sophisticated hacking methods. These methods range from exploiting vulnerabilities in software to leveraging psychological manipulation. Criminals are constantly innovating, adapting their techniques to overcome existing security measures. This necessitates a proactive approach to security by e-commerce businesses.
Methods to Steal Customer Data
Criminals employ diverse techniques to acquire sensitive customer data, ranging from subtle phishing campaigns to sophisticated malware installations. The primary goal is to gain unauthorized access to user accounts and financial information. Phishing emails, masquerading as legitimate communications, are a common method, luring unsuspecting customers into revealing their credentials.
Methods to Disrupt Services
Beyond data theft, hackers also aim to disrupt e-commerce services through various means. Denial-of-service (DoS) attacks, flooding servers with traffic, are a common tactic to make online stores inaccessible. This can lead to significant financial losses and reputational damage for the businesses.
Attack Vectors
The table below highlights common attack vectors targeting e-commerce platforms. It is important to recognize the diversity and sophistication of these attacks.
| Attack Vector | Description | Impact |
|---|---|---|
| Phishing | Deceptive emails, websites, or messages designed to trick users into revealing sensitive information like usernames, passwords, or credit card details. | Data breaches, financial losses, and reputational damage. |
| Malware | Malicious software designed to infiltrate systems, steal data, or disrupt operations. This includes viruses, Trojans, and ransomware. | Data breaches, system compromise, and potential financial losses. |
| Denial-of-Service (DoS) Attacks | Overwhelming a website or online service with traffic, making it unavailable to legitimate users. | Loss of revenue, reputational damage, and disruption of operations. |
| SQL Injection | Exploiting vulnerabilities in database queries to gain unauthorized access to sensitive information or manipulate data. | Data breaches, data manipulation, and potential system compromise. |
Frequency and Sophistication of Recent Attacks
Recent attacks on e-commerce platforms have demonstrated an increasing frequency and sophistication. Hackers are employing more advanced techniques, including automated tools and coordinated attacks, making it harder for businesses to detect and respond to threats. This highlights the need for robust security measures and continuous monitoring. Examples include the rise in targeted phishing campaigns against specific customer segments or the use of sophisticated malware that can evade traditional detection methods.
Psychological Factors Behind Hacker Motivations
The motivations behind hacker activities are multifaceted and often driven by a combination of factors, including financial gain, ego satisfaction, and a desire for notoriety. Sometimes, hackers act out of ideological or political motives, targeting specific businesses or organizations. The psychological motivations are as complex as the methods employed in these attacks.
Security Measures and Vulnerabilities

E-commerce platforms, while offering convenience and global reach, are increasingly vulnerable to sophisticated attacks. Understanding the vulnerabilities and security measures employed is crucial for businesses to protect themselves and maintain customer trust. This section delves into common weaknesses, current security protocols, and the vital role of secure payment gateways.Modern e-commerce systems face a multitude of threats, from straightforward credit card fraud to complex data breaches.
This necessitates a multifaceted approach to security, encompassing various layers and technologies. The evolving nature of these attacks necessitates continuous adaptation and improvement in security strategies.
Common Security Vulnerabilities in E-commerce Systems
E-commerce systems face various vulnerabilities, including those in web applications, databases, and network infrastructure. Cross-site scripting (XSS) attacks, SQL injection, and insecure APIs are common avenues for malicious actors to exploit weaknesses and gain unauthorized access. These vulnerabilities can compromise customer data, financial information, and even the integrity of the entire platform. Insufficient input validation, weak authentication mechanisms, and outdated software are contributing factors.
Current Security Measures Employed by E-commerce Businesses
Modern e-commerce businesses utilize a range of security measures to protect their platforms and customer data. These include robust firewalls, intrusion detection systems, and regular security audits. Advanced encryption techniques, such as Transport Layer Security (TLS), are implemented to safeguard sensitive data during transmission. Security awareness training for employees plays a crucial role in preventing phishing attacks and other social engineering tactics.
The latest hacker attacks are really shaking up the e-commerce world, causing a ripple effect across various businesses. Meanwhile, CMGI, a company often overlooked in this digital storm, just blasted past earnings estimates, showing surprising resilience in the face of these growing security threats. This strong performance, detailed in their recent earnings report ( cmgi blasts past earnings estimate ), might indicate a shift in how companies are handling the risks of e-commerce hacking.
Still, the constant threat of cyberattacks remains a major concern for online retailers.
Multi-factor authentication (MFA) adds an extra layer of security by requiring multiple verification steps before granting access.
Securing Payment Gateways
Secure payment processing is paramount for e-commerce businesses. Payment gateways are designed with robust security measures, including encryption protocols like TLS and secure sockets layer (SSL). These protocols ensure that sensitive financial information is transmitted confidentially and cannot be intercepted. Regular audits and penetration testing are essential to identify potential weaknesses and ensure the security of payment gateways.
Strict adherence to industry standards and regulations like PCI DSS (Payment Card Industry Data Security Standard) is critical for protecting payment information.
The latest hacker attacks are rattling e-commerce, causing serious disruptions. Meanwhile, it’s good to see companies like Borders, with their “Borders.com about .com enjoy big week together” event, are still finding ways to connect with customers. These events are a welcome distraction from the current anxieties surrounding e-commerce security and show that even with ongoing threats, the industry continues to innovate and engage with consumers.
However, the question remains, how will e-commerce platforms maintain trust and user confidence amidst the ongoing wave of attacks? borders com about com enjoy big week together
Comparison of Security Protocols
Different security protocols offer varying levels of protection. For instance, TLS 1.3 provides enhanced security compared to earlier versions, offering stronger encryption and improved performance. The effectiveness of a protocol depends on its implementation, the quality of the underlying infrastructure, and the regular updates. Proper configuration and maintenance are essential to maximize the security provided by these protocols.
Different Layers of Security, Latest hacker attacks rattle e commerce
Security measures are implemented across various layers of an e-commerce system. The effectiveness of security depends on the robust implementation and constant monitoring of all layers.
| Layer | Description | Examples |
|---|---|---|
| Network Layer | Protecting the network infrastructure from unauthorized access and attacks. | Firewalls, intrusion detection systems, network segmentation |
| Application Layer | Securing the applications themselves from vulnerabilities like SQL injection and cross-site scripting. | Input validation, secure coding practices, web application firewalls (WAFs) |
| Data Layer | Protecting sensitive data at rest and in transit, using encryption and access controls. | Data encryption, access controls, secure databases |
Customer Response and Actions
E-commerce businesses face significant challenges when a security breach occurs. Beyond the immediate financial and reputational damage, the fallout often manifests in customer reactions that can significantly impact future sales and trust. Understanding these reactions is crucial for retailers to formulate effective recovery strategies and maintain customer loyalty. Customer responses vary widely, ranging from complaints and boycotts to a gradual erosion of trust, highlighting the importance of swift and transparent communication.Customer perceptions of security breaches are multifaceted and often involve a complex interplay of emotions.
Loss of trust in a retailer can be particularly damaging, potentially leading to long-term consequences for the business. The speed and thoroughness of the retailer’s response, including the steps taken to rectify the breach and reassure customers, play a critical role in shaping customer perceptions.
Customer Reactions to Security Breaches
Customer reactions to security breaches often involve a range of emotions and behaviors. Customers may feel a sense of vulnerability, leading to apprehension and distrust towards the online retailer. This distrust can manifest in a variety of ways, including reduced willingness to shop, increased skepticism about the security measures in place, and a general reluctance to provide personal information.
Impact on Shopping Habits
Security breaches can significantly alter customer shopping habits. Customers who have experienced a breach may be more cautious in the future, scrutinizing online retailers’ security practices more rigorously. This increased scrutiny can lead to customers seeking out alternative online retailers perceived as more secure. Reduced purchases and a shift to alternative platforms are direct consequences of the negative experience associated with the breach.
Examples of Customer Responses
Negative customer responses to security breaches can vary from simple complaints to more severe actions, like boycotts. Complaints often focus on the lack of transparency in the retailer’s response or the perceived inadequacy of security measures. Boycotts are a more extreme reaction, where customers actively choose to avoid the retailer’s platform altogether, opting for competitors. This can have a devastating impact on the retailer’s revenue and reputation.
Assessing Retailer Reliability and Security
Customers evaluate the reliability and security of online retailers based on a multitude of factors. Beyond the retailer’s publicized security measures, customers consider the retailer’s past performance, the frequency and severity of past security incidents, and the retailer’s response to these incidents. The retailer’s reputation and history play a vital role in shaping customer trust.
Customer Feedback on E-commerce Platforms
Customer feedback following security breaches varies widely depending on the specific platform and the severity of the breach. This variability highlights the importance of personalized and tailored responses.
| E-commerce Platform | Customer Feedback (Example) |
|---|---|
| Retail Giant A | High volume of complaints, some boycotts. Customers expressed distrust in the retailer’s security measures. |
| Boutique B | Relatively fewer complaints. Customers praised the retailer’s swift and transparent response. |
| Startup C | Mixed feedback. Customers appreciated the initial communication but criticized the lack of a long-term security plan. |
Future Trends in E-commerce Security
The digital landscape is constantly evolving, and e-commerce businesses must adapt their security strategies to stay ahead of emerging threats. Predicting the future is challenging, but analyzing current trends and potential vulnerabilities allows businesses to proactively implement robust defenses. This proactive approach is crucial for safeguarding customer data and maintaining trust in the online marketplace.The evolving cyber security threat landscape is characterized by increasing sophistication and frequency of attacks.
Sophisticated hacking techniques, coupled with the rise of AI-powered tools, pose a significant risk to e-commerce platforms. The potential for data breaches, financial fraud, and reputational damage underscores the critical need for continuous security improvements.
Potential Future Threats and Attacks
The nature of cyberattacks is constantly changing. Emerging threats include sophisticated phishing campaigns leveraging AI-generated content, and supply chain attacks targeting vulnerabilities in third-party vendors. These attacks often exploit the growing interconnectedness of e-commerce systems and their reliance on various software and platforms. Furthermore, the increasing use of the Internet of Things (IoT) devices in e-commerce operations introduces new attack vectors.
For instance, a compromised smart device could potentially gain access to sensitive data or disrupt critical operations.
Evolving Landscape of Cyber Security Threats
The sophistication of cyberattacks is escalating. Attacks are becoming more targeted, leveraging sophisticated techniques like social engineering and exploiting zero-day vulnerabilities. The growing interconnectedness of e-commerce systems and their dependence on third-party services and software create new avenues for attack. Moreover, the use of AI-powered tools is enabling attackers to create more sophisticated and personalized phishing campaigns, making it harder for users to identify malicious communications.
Development of Advanced Security Measures
Businesses must implement advanced security measures to combat evolving threats. This includes the deployment of advanced threat detection systems capable of identifying and responding to sophisticated attacks in real time. Robust multi-factor authentication (MFA) protocols are essential for protecting user accounts. Additionally, encryption plays a critical role in safeguarding sensitive data during transmission and storage. Continuous security audits and penetration testing are crucial for identifying and mitigating potential vulnerabilities.
Emerging Technologies and Their Role
Emerging technologies, such as blockchain and AI, offer new opportunities for bolstering e-commerce security. Blockchain technology can enhance the security and transparency of transactions. AI can be used to detect anomalies and suspicious patterns in user activity, helping to prevent fraud and malicious attacks. Furthermore, machine learning algorithms can be employed to identify and classify evolving threats, enabling proactive security measures.
Projected Growth of Security Threats (Next 5 Years)
| Threat Type | Projected Growth (Estimated Percentage Increase) |
|---|---|
| AI-powered phishing campaigns | 45-60% |
| Supply chain attacks | 30-45% |
| IoT device-based attacks | 25-40% |
| Sophisticated ransomware attacks | 35-55% |
| Zero-day exploits | 20-35% |
Note: Projections are based on current trends and potential future developments in the technology and threat landscape.
Regulatory and Legal Landscape: Latest Hacker Attacks Rattle E Commerce
The e-commerce landscape is increasingly governed by a complex web of regulations and legal frameworks. These regulations are crucial for maintaining consumer trust and protecting businesses from liability, particularly in the wake of escalating cyber threats. Understanding these legal intricacies is essential for e-commerce companies to navigate the evolving digital environment and mitigate potential risks.
Regulatory Frameworks Surrounding E-commerce Security
Various legal frameworks dictate how e-commerce businesses must handle security matters. These frameworks encompass data protection, breach notification, and other related aspects. Governments worldwide are recognizing the importance of online security and implementing legislation to address the vulnerabilities inherent in digital commerce. This includes mandates for robust security measures, incident response plans, and consumer notification procedures.
Legal Implications for E-commerce Businesses After Security Breaches
Security breaches can have significant legal ramifications for e-commerce businesses. Failure to comply with relevant regulations can result in substantial fines, legal action, and reputational damage. Breaches exposing sensitive customer data, such as financial information or personally identifiable information (PII), can lead to lawsuits from affected individuals. The legal implications can be severe, impacting not only the company’s financial health but also its long-term viability.
Data Privacy Regulations
Data privacy regulations like GDPR (General Data Protection Regulation) and CCPA (California Consumer Privacy Act) play a critical role in e-commerce security. These regulations Artikel the rights of consumers regarding their personal data and impose obligations on businesses to protect that data. Failure to adhere to these regulations can lead to substantial penalties and reputational harm.
Potential Liabilities for Companies Experiencing Attacks
E-commerce businesses face potential liabilities if they fail to implement adequate security measures. This includes financial penalties, legal action, and reputational damage. The scope of liability can vary depending on the nature of the breach, the extent of data compromised, and the specific regulations applicable to the jurisdiction. For example, a breach that exposes customer credit card information could result in significant financial and legal repercussions.
Key Regulations and Their Impact on E-commerce Security
| Regulation | Impact on E-commerce Security |
|---|---|
| GDPR (General Data Protection Regulation) | Requires businesses to implement appropriate technical and organizational measures to protect personal data, mandates breach notification requirements, and empowers individuals with data subject rights. |
| CCPA (California Consumer Privacy Act) | Grants California residents specific rights regarding their personal data, including the right to know, delete, and opt-out of the sale of their personal information. It imposes obligations on businesses to implement security measures and provide transparency to consumers. |
| HIPAA (Health Insurance Portability and Accountability Act) | Applies to e-commerce businesses handling protected health information (PHI). It mandates stringent security protocols and data privacy safeguards. |
| PCI DSS (Payment Card Industry Data Security Standard) | Requires businesses handling credit card information to implement specific security measures to protect cardholder data. Failure to comply with these standards can result in severe penalties and financial losses. |
Protecting Customer Data and Information
Protecting customer data is paramount in the e-commerce landscape. Breaches not only damage a company’s reputation but also expose customers to significant financial and personal risks. This necessitates a robust approach to data encryption, secure storage, and transmission protocols. Implementing these measures builds trust and safeguards the sensitive information of online shoppers.E-commerce platforms handle vast amounts of customer data, including personally identifiable information (PII), financial details, and browsing history.
The security of this data is crucial for maintaining customer trust and avoiding costly legal and reputational damage. Effective protection involves a multi-layered approach that addresses data at rest (stored data) and in transit (data being transferred).
Importance of Customer Data Protection
Robust data protection safeguards customer trust, fosters a positive brand image, and minimizes legal and financial risks. A data breach can lead to significant financial penalties, reputational damage, and a loss of customer confidence. Companies with strong data protection measures often attract and retain customers more effectively.
Methods for Encrypting and Safeguarding Customer Data
Data encryption is a fundamental technique for safeguarding sensitive customer information. Various encryption methods, such as Advanced Encryption Standard (AES), are used to transform data into an unreadable format, preventing unauthorized access. Strong passwords, multi-factor authentication, and regular security audits are also crucial elements in protecting customer data.
Secure Data Storage and Transmission Protocols
Secure data storage involves employing robust systems and technologies to protect data at rest. This includes using encryption at the storage level, restricting access to authorized personnel, and implementing regular backups. Secure transmission protocols, such as Transport Layer Security (TLS), are critical for protecting data during transit. TLS encrypts data exchanged between the customer’s browser and the e-commerce website, preventing eavesdropping.
Best Practices for Securing Customer Data
- Regular Security Audits: Conducting periodic security audits helps identify vulnerabilities and implement necessary fixes to prevent breaches. Regular audits ensure that systems and processes remain up-to-date with evolving threats.
- Data Minimization: Collecting only the necessary data helps reduce the attack surface. Only collecting the required customer data is a strong preventative measure.
- Access Control: Implementing strict access control measures limits access to sensitive data to authorized personnel. Restricting access to only necessary personnel is a critical security measure.
- Employee Training: Educating employees on data security best practices helps prevent human error-related breaches. Regular training sessions ensure employees understand the importance of security protocols.
- Incident Response Plan: Having a well-defined incident response plan ensures a swift and organized response in case of a data breach. Having a documented plan is crucial for a rapid and effective response.
Role of Encryption Technologies in Mitigating Risks
Encryption technologies play a crucial role in mitigating risks by transforming data into an unreadable format, making it unusable for unauthorized individuals. This prevents unauthorized access to sensitive information, even if the data is intercepted. Robust encryption algorithms and protocols are essential for safeguarding data and maintaining customer trust. Modern e-commerce platforms utilize encryption to protect customer data during both storage and transmission.
| Best Practice | Description |
|---|---|
| Strong Passwords | Use complex passwords with a combination of uppercase and lowercase letters, numbers, and symbols. |
| Multi-Factor Authentication | Implement multi-factor authentication to add an extra layer of security. |
| Regular Software Updates | Keep software and systems up-to-date with the latest security patches. |
| Firewall Protection | Employ firewalls to block unauthorized access to the network. |
| Secure Payment Gateways | Use secure payment gateways to protect customer financial information. |
Wrap-Up
In conclusion, the latest hacker attacks underscore the critical need for robust security measures in the e-commerce industry. From preventative strategies to reactive responses, companies must prioritize security to safeguard their financial well-being and maintain customer trust. The evolving nature of these threats necessitates continuous adaptation and investment in cutting-edge security technologies. This is a crucial moment for the industry to adapt and mitigate future risks.






