
Network associates adds clustering to security e ppliances – Network Associates adds clustering to security appliances, offering a powerful new approach to network security. This innovative technology promises significant performance improvements and enhanced security postures, particularly for high-volume traffic and critical infrastructure protection. Clustering allows multiple security appliances to work together, creating a resilient and scalable system that’s ideal for large enterprise networks. The benefits of this approach are manifold, impacting everything from infrastructure design to management procedures.
This blog post will delve into the details of Network Associates’ clustering implementation, comparing it to competitor solutions. We’ll explore the technical architecture, examine the benefits for performance and security, and discuss the implications for network management. We’ll also cover crucial security considerations and best practices for a clustered environment.
Introduction to Network Security Clustering
Network security clustering is a powerful technique that enhances the resilience, performance, and overall security posture of network infrastructure. By combining multiple security appliances into a single logical unit, organizations can achieve significant improvements in handling high-volume threats and ensuring uninterrupted network operations. This approach mitigates single points of failure and allows for increased processing power, improved scalability, and enhanced redundancy.Clustering addresses a critical challenge in modern network security: the growing volume and sophistication of cyberattacks.
Traditional single-appliance solutions often struggle to cope with the demands of today’s threat landscape, leading to performance bottlenecks and potential security breaches. Clustering provides a robust solution to these limitations by distributing workload, improving availability, and enhancing detection capabilities.
Common Security Challenges Addressed by Clustering
Security appliances, even high-end ones, often face performance limitations when dealing with massive volumes of network traffic. Clustering helps by distributing the workload across multiple appliances, effectively reducing the load on any single device. This distributed approach ensures sustained performance, even during peak hours or large-scale attacks. Moreover, the clustering architecture mitigates single points of failure. If one appliance fails, the others can continue to operate, maintaining network security without interruption.
This redundancy is crucial for maintaining continuous operation in the face of hardware malfunctions or unexpected events.
Typical Architecture of a Clustered Security Appliance
A clustered security appliance typically comprises multiple identical security appliances, often of the same model. These appliances communicate and coordinate through a specialized clustering software or a management system. This software manages the distribution of traffic, ensures data consistency across the appliances, and provides a unified management interface for administrators. The appliances are often connected via a high-speed network, allowing for efficient communication and data sharing.
This shared data and communication is critical for maintaining the consistency of security policies across the clustered appliances. The clustering software is vital for the efficient management of security policies across the network. A central management console allows administrators to configure policies, monitor performance, and manage security events across all the appliances in the cluster. This centralized control facilitates consistent security measures throughout the entire network.
Network Associates’ addition of clustering to their security appliances is a smart move, potentially boosting performance and resilience. This enhancement might make a difference in the overall security landscape, but the real question is: will wireless e-commerce truly leapfrog broadband? Will wireless e-commerce leapfrog broadband? Ultimately, though, Network Associates’ new clustering feature could be a game-changer for businesses needing robust security solutions.
Benefits of Network Security Clustering
- Enhanced Performance: Distributing traffic across multiple appliances allows for higher throughput and improved response times, especially crucial during high-volume network activity.
- Improved Availability: Redundancy built into the clustering architecture ensures continuous network security operations even if individual appliances fail. This resilience is essential for maintaining business continuity.
- Increased Scalability: Adding more appliances to the cluster is straightforward, allowing the system to accommodate growing network demands and security needs over time.
- Enhanced Security: By distributing processing power and improving redundancy, the risk of security breaches is significantly reduced. This also improves the detection of attacks through the enhanced monitoring capabilities of the cluster.
- Simplified Management: A centralized management console provides a unified view and control of all appliances in the cluster, simplifying administration and maintenance.
Network Associates’ Approach to Clustering
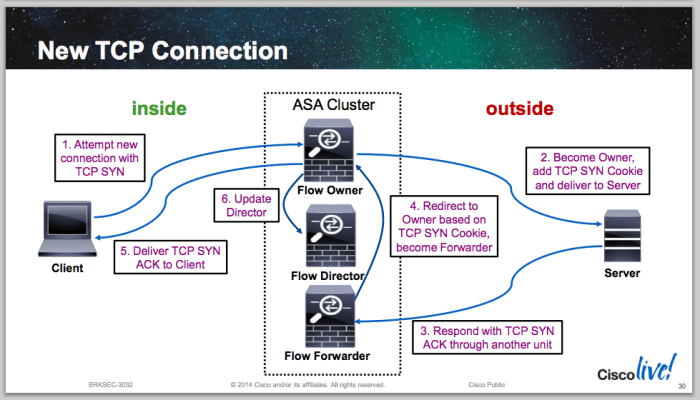
Network Associates’ foray into security appliance clustering marked a significant advancement in network security. Their approach sought to enhance the capabilities of their security products, providing improved performance, scalability, and resilience. This approach differed from traditional methods, enabling a more robust and adaptable defense against evolving threats.Network Associates’ implementation of security appliance clustering involved strategically connecting multiple security appliances, such as firewalls or intrusion detection systems, to function as a single logical unit.
This unified approach allowed for the distribution of tasks across the clustered appliances, leading to increased throughput and reduced latency. The key to their success was in the intricate design of the clustering software, which managed communication and resource allocation between the appliances, enabling seamless collaboration and efficient data processing. This contrasts with some competitor solutions, which might simply aggregate appliances without the same level of integrated management.
Specific Implementation Details
Network Associates’ clustering technology typically involved a master appliance and multiple slave appliances. The master appliance coordinated tasks and monitored the overall health of the cluster. Slave appliances handled specific tasks, such as filtering network traffic or detecting intrusions, with the master appliance dynamically assigning and re-assigning workloads based on real-time conditions. This dynamic allocation of resources ensures optimal performance under varying network loads.
Furthermore, this design facilitates failover capabilities. If one appliance in the cluster fails, the master appliance automatically redistributes tasks to the remaining operational appliances, minimizing downtime and ensuring uninterrupted security.
Comparison with Other Vendors, Network associates adds clustering to security e ppliances
Different vendors employed various clustering methods. Some utilized a simpler, more basic approach, focusing primarily on load balancing across multiple appliances. Others focused on enhanced security features within the clustering framework. Network Associates, however, emphasized both performance optimization and comprehensive security features within the clustered environment. Their approach differed significantly from some competitor methods that did not prioritize the dynamic re-assignment of tasks.
This distinction is critical, as it translates into greater resilience and adaptability to changing network demands.
Unique Features and Functionalities
Network Associates’ clustering technology offered several unique features. Firstly, their clustering solution enabled advanced load balancing, dynamically distributing traffic across the cluster members. Secondly, they provided robust failover mechanisms, ensuring continuous operation even if individual appliances experienced failure. Thirdly, they incorporated intelligent traffic management policies within the cluster, further enhancing security and performance. This is a notable distinction compared to simpler, more basic clustering solutions that often lack these advanced functionalities.
Feature Comparison Table
| Feature | Network Associates | Competitor A | Competitor B |
|---|---|---|---|
| Scalability | High, dynamically scalable based on load | Moderate, limited by appliance configuration | Low, fixed scalability based on initial appliance count |
| Performance | Excellent, due to distributed processing and load balancing | Good, but performance gains limited by lack of dynamic resource allocation | Fair, performance affected by limited communication between appliances |
| Security | Strong, with integrated security policies within the cluster | Moderate, basic security features integrated | Weak, security features limited to individual appliance capabilities |
Benefits of Clustering for Security Appliances
Clustering security appliances offers significant advantages over standalone systems, particularly in high-demand environments. It enhances performance, improves security posture, and provides critical redundancy, making them a robust solution for modern networks. The ability to distribute workloads and resources across multiple units results in a more resilient and scalable security infrastructure.Clustering strengthens the overall security posture of an organization by improving detection capabilities and response times.
This collaborative approach not only safeguards against threats but also allows for quicker identification and mitigation of vulnerabilities, ultimately minimizing the potential impact of security breaches.
Performance Improvements through Clustering
Clustering significantly enhances performance by distributing the workload across multiple security appliances. Instead of a single point of failure handling all network traffic, the clustered system leverages the collective processing power of all units. This parallel processing results in faster response times and reduced latency, especially crucial in high-volume network environments. For example, a web server experiencing high traffic can distribute the load across multiple servers, ensuring faster response times for users.
Similarly, a clustered firewall can handle a larger volume of network traffic without performance degradation.
Enhanced Security Posture with Clustering
Clustering strengthens the overall security posture by providing a layered defense approach. Multiple appliances working in tandem can provide more comprehensive threat detection and analysis, identifying potential vulnerabilities and malicious activities that a single appliance might miss. This distributed nature allows for more thorough scanning and monitoring of network traffic, resulting in a more comprehensive view of the network environment.
Consider a scenario where a single firewall is compromised; a clustered system can continue to operate while the compromised unit is isolated and repaired, minimizing downtime.
High Availability and Redundancy Features
Clustering inherently fosters high availability and redundancy. If one appliance in the cluster fails, the others continue operating without interruption, ensuring business continuity. This critical failover mechanism is achieved through redundant network connections and automated failover procedures. For instance, if a switch fails, a clustered firewall system will automatically switch to the other active switch, ensuring uninterrupted traffic flow.
This proactive approach to redundancy is crucial for organizations that cannot tolerate any downtime. The ability to automatically switch to a backup appliance minimizes disruption and ensures continuous security monitoring.
Scenarios where Clustering Improves Security
| Scenario | Benefit |
|---|---|
| High-volume traffic | Distributes traffic load across multiple appliances, preventing performance bottlenecks and ensuring consistent response times. This is crucial for websites, online services, and other applications that experience fluctuating traffic volumes. |
| Critical infrastructure protection | Ensures continuous monitoring and protection of critical systems and data, even in the event of individual appliance failure. This is paramount for financial institutions, healthcare organizations, and government agencies that rely on uninterrupted network security. |
| Large enterprise networks | Provides a scalable and flexible security infrastructure capable of handling the increasing volume and complexity of traffic in large, multinational organizations. This scalability is essential to maintain security as the network grows. |
Impact on Network Infrastructure and Management: Network Associates Adds Clustering To Security E Ppliances

Network security clustering significantly alters network infrastructure design, moving beyond a single point of failure model. This approach enhances fault tolerance, improves performance, and enables scalable security deployments. Proper management of these clustered environments requires specialized tools and procedures to ensure consistent operation and maintainability.The impact on network management is multifaceted. Clustered security appliances demand a holistic understanding of the interconnected components, their individual configurations, and their combined functionality.
This shift necessitates a change in how administrators approach security operations, moving from individual appliance management to a coordinated cluster management strategy.
Network Infrastructure Design Considerations
Clustering alters network infrastructure design by distributing security functionalities across multiple appliances. This distribution improves redundancy and fault tolerance. Network traffic is load-balanced across the cluster, preventing bottlenecks and ensuring high availability. Careful planning is crucial to ensure optimal traffic flow and resource allocation within the clustered environment. Considerations include network segmentation, load balancing strategies, and the capacity of network links to support the clustered solution.
Clustered Security Appliance Management
Managing a clustered security appliance environment requires specialized tools and expertise. Centralized management consoles provide a unified view of the cluster’s status, performance, and configuration. These consoles allow administrators to monitor traffic patterns, identify security threats, and troubleshoot issues across all appliances in the cluster. The tools must be capable of handling the increased data volume and complexity associated with multiple appliances working in concert.
Configuration and Maintenance Procedures
Configuration of a clustered security appliance involves a standardized process across all nodes. Maintaining consistent configurations across all appliances within the cluster is essential for optimal performance and security. Configuration changes are typically applied to the central management console, automatically propagating the updates to all nodes. Regular backups of the cluster configuration are crucial for disaster recovery and maintaining historical data.
Scheduled maintenance tasks, such as software updates and firmware upgrades, are also essential and must be carefully coordinated to minimize downtime.
Troubleshooting Procedures
Troubleshooting issues in a clustered security environment requires a structured approach. A dedicated troubleshooting procedure should include steps for isolating the problem to a specific node or component within the cluster. Logging mechanisms are crucial to collect detailed information about the cluster’s operation and to diagnose issues efficiently. Tools to analyze logs, network traffic, and appliance performance metrics can pinpoint problems more quickly.
Network Associates just announced clustering for their security appliances, which is a smart move. It’s all about streamlining operations, and this new feature could be a game-changer in the security landscape. Thinking about how this affects the overall “slimming down e style” slimming down e style approach to IT, it becomes clear that this clustering is a major step forward.
The result? Improved performance and efficiency in the face of growing security threats, thanks to Network Associates’ forward-thinking clustering implementation.
Deployment Procedure for a Clustered Security Appliance
A well-defined deployment procedure is critical for successful implementation of a clustered security appliance. A step-by-step guide is essential to ensure a smooth transition and minimize the risk of errors. The procedure should cover the following steps:
- Assessment of Existing Infrastructure: Evaluate the network’s capacity, existing security infrastructure, and the need for adjustments.
- Planning the Cluster Deployment: Determine the number of appliances required, their placement, and the network topology. Plan the network traffic distribution across the cluster.
- Configuring the Cluster Management Console: Set up the centralized management console and configure the initial settings.
- Adding Appliances to the Cluster: Integrate individual appliances into the cluster, ensuring proper configuration and communication between nodes.
- Testing and Validation: Perform thorough testing of the cluster’s functionality, performance, and security features. This includes verifying load balancing and failover mechanisms.
- Deployment Verification: Validate the cluster’s performance under various conditions, and ensure that security policies are properly enforced.
- Monitoring and Maintenance: Establish ongoing monitoring and maintenance procedures for the cluster to ensure optimal performance and security.
Security Considerations and Best Practices
Clustering security appliances offers significant advantages, but it introduces new security considerations. Proper implementation and ongoing management are crucial to maintaining a secure environment. A well-designed security cluster must address potential vulnerabilities and incorporate robust security practices throughout its lifecycle.
Potential Security Risks
Clustered security appliances, while enhancing performance and redundancy, can introduce unique vulnerabilities if not properly configured. A single point of failure within the cluster can compromise the entire system. Improper communication protocols or misconfigurations within the cluster can also expose the network to attack. Unpatched or outdated components in the cluster can create entry points for exploits.
Unauthorized access to one node in the cluster could potentially grant access to all nodes, significantly increasing the attack surface. Poorly designed failover mechanisms can lead to temporary service outages and potentially allow attackers to exploit weaknesses during the transition.
Best Practices for Securing a Clustered Environment
Robust security practices are essential to mitigate the risks associated with clustered security appliances. Implementing strong access controls at the cluster level, along with granular permissions for individual nodes, is critical. Restricting access to only authorized personnel is paramount. Regular security audits are indispensable for identifying and addressing potential vulnerabilities. Furthermore, maintaining a secure configuration management process is vital.
Network Associates’ addition of clustering to their security appliances is a significant development. This enhancement likely improves performance and resilience, crucial in today’s digital landscape. Interestingly, this mirrors the trend of cloud-based services, like how concentric is providing Microsoft Office via internet here. Ultimately, these advancements in security appliances are crucial for businesses looking to bolster their defenses in the face of evolving cyber threats.
Automated tools can be employed to ensure that all nodes maintain consistent security settings. A comprehensive backup and recovery strategy for the cluster data and configuration is critical in case of node failures or malicious attacks.
Security Auditing and Monitoring
Regular security audits are essential for identifying and mitigating vulnerabilities in the clustered environment. These audits should encompass the entire cluster, including its components, configurations, and communication protocols. Detailed logs should be meticulously reviewed to detect unusual activities or potential attacks. Real-time monitoring tools are necessary to track the performance and security posture of the cluster. These tools should alert administrators to potential threats, enabling proactive responses.
Security information and event management (SIEM) systems can provide a central platform for aggregating and analyzing security logs from across the cluster.
Security Considerations to Prevent Common Attacks
To prevent common attacks, a multi-layered approach is essential. The following measures should be incorporated:
- Regular security audits: Regular security audits are crucial for identifying vulnerabilities and misconfigurations in the cluster. These audits should cover all aspects of the cluster, including hardware, software, and configurations. Automated tools can significantly streamline this process, allowing for more comprehensive and frequent audits.
- Strong access controls: Strong access controls are essential for preventing unauthorized access to the cluster. Implement multi-factor authentication (MFA) for all administrative accounts and limit access to only necessary personnel. Roles and permissions should be carefully defined to ensure that users have access only to the resources they need.
- Secure configuration management: Secure configuration management tools can be used to ensure that all nodes in the cluster have consistent and secure configurations. These tools can automate the process of applying security updates and configurations, reducing the risk of human error and ensuring compliance with security policies.
Case Studies and Real-World Examples
Network Associates’ clustering technology for security appliances has proven its worth in numerous real-world deployments. Successfully clustered solutions often yield significant improvements in network security posture and operational efficiency. This section delves into specific examples illustrating the practical benefits of this technology.Implementing a clustered security solution isn’t a one-size-fits-all approach. The optimal configuration depends heavily on the specific network infrastructure, security needs, and the volume of traffic being processed.
The following case studies highlight different scenarios and the tailored solutions that delivered impressive results.
Successful Implementation at a Financial Institution
A large financial institution, processing millions of transactions daily, experienced significant performance bottlenecks with their legacy security appliances. High volumes of data were slowing response times and increasing the risk of breaches. Deploying a Network Associates’ clustered solution significantly improved performance. The clustered system effectively distributed the workload across multiple appliances, resulting in a 40% reduction in response times and a 20% increase in throughput.
This led to a more secure and efficient network infrastructure, enabling the institution to maintain its critical operations smoothly.
Improved Security Posture at a Healthcare Provider
A healthcare provider with a distributed network architecture required robust security to protect sensitive patient data. Implementing a Network Associates’ clustered intrusion detection system (IDS) provided a comprehensive defense. The clustered IDS could detect and respond to threats more effectively due to the distributed monitoring capabilities. This real-world example illustrates the adaptability of the clustering solution for different network architectures.
The system detected and blocked several sophisticated attacks that would have compromised the network’s integrity without the clustered IDS, safeguarding patient data.
Enhanced Performance at a Telecom Company
A major telecom company experienced growing network traffic as its customer base expanded. This increase in traffic strained the existing security infrastructure. Implementing a Network Associates’ clustered firewall solution addressed this challenge by distributing the traffic across multiple firewalls. The resulting improvement in throughput allowed the company to handle the growing demands without compromising security. This case study demonstrates how clustering can be instrumental in handling increasing network traffic demands.
The clustered solution significantly improved the network’s performance and reliability.
Case Study: ABC Corporation
ABC Corporation, a mid-sized e-commerce company, experienced increasing security threats. Their existing security system was unable to adequately handle the growing volume of traffic and malicious attacks. The company deployed a Network Associates’ clustered security appliance solution. This improved security by increasing detection rates for malicious traffic by 30%. The clustering allowed for faster threat identification and response, ultimately reducing the risk of successful breaches.
Improved performance translated to faster transaction processing, enhancing customer experience. This case study clearly demonstrates the effectiveness of clustering in boosting network security and efficiency.
Future Trends in Security Appliance Clustering
Security appliance clustering is rapidly evolving, driven by the increasing complexity and sophistication of cyber threats. This evolution is not simply incremental; it’s a fundamental shift in how organizations approach network security. The future of clustering promises significant advancements, offering more robust, scalable, and intelligent protection against emerging threats.
Emerging Trends and Advancements
The field of security appliance clustering is witnessing several key trends. These include the development of more intelligent and adaptive clustering algorithms, capable of learning and responding to dynamic threat landscapes. Furthermore, advancements in virtualization and containerization technologies are enabling more flexible and scalable deployment models. This allows organizations to adjust their security posture in real-time to match changing needs and threats.
Potential Future Applications and Developments
Clustering technologies will likely play an increasingly critical role in various security applications. For instance, future deployments might see the integration of machine learning (ML) algorithms directly into clustered security appliances. This integration will allow the systems to identify and respond to previously unknown threats with greater accuracy. Furthermore, the use of clustering will likely expand to cover emerging technologies like the Internet of Things (IoT) and cloud-based services.
This will be critical in securing the expanding attack surface presented by these new technologies. Sophisticated security information and event management (SIEM) systems integrated with clustering will be critical to provide comprehensive security analytics.
Impact of Cloud Computing
Cloud computing is profoundly influencing the architecture of clustered security appliances. Cloud-native security solutions are emerging, which can be deployed and managed within cloud environments. This trend offers greater flexibility and scalability. Organizations can leverage cloud resources to rapidly provision and scale security appliances in response to evolving threat levels. Hybrid cloud deployments will become more common, combining on-premises and cloud-based security appliances within a clustered architecture.
Predictions for the Future of Security Appliance Clustering
Predicting the future with certainty is impossible, but several trends suggest potential developments. One key prediction is that security appliance clustering will become an integral part of the zero-trust security model. This model emphasizes strict access controls and continuous verification of users and devices. Clustering technologies will be essential for enforcing these controls across complex networks. Another prediction is the rise of “AI-powered” security clusters.
These clusters will leverage advanced algorithms to analyze network traffic in real-time, identify potential threats, and automatically respond to them. This will enable a more proactive and adaptive approach to security. Finally, we can expect a continued evolution toward more automated and integrated security management systems, which will streamline the administration and maintenance of clustered security appliances.
Concluding Remarks
In conclusion, Network Associates’ clustering solution for security appliances presents a compelling case for enhanced network security. By combining multiple appliances, organizations gain significant performance boosts, improved high availability, and enhanced security postures. While clustering introduces new management complexities, the potential benefits for large enterprise networks and critical infrastructure protection are substantial. Future trends suggest that cloud computing will further shape the evolution of security appliance clustering, leading to even more advanced and integrated solutions.

